-
Posts
9260 -
Joined
-
Last visited
-
Days Won
371
Everything posted by anyweb
-
I'm not doing a feature upgrade, i'm installing an os fresh and including 2 language packs+regional settings as part of that, and it's that part you are interested in right ?
-

SCCM BitLocker in MDT Task Sequence
anyweb replied to ace_ventura's question in Microsoft Deployment Toolkit (MDT)
For this to work you'll need the configmgr client agent installed on the computers, will it be ? -
i'm building this in my lab at the moment, i will get it all working there before i blog it, so hopefully within a day or two.
-
the way I implemented it was based on detection of location via a dynamic variables in the task sequence, you could base it on many things such as dhcp ip address, collection variable, computer variable(s) etc, then in the task sequence apply both the english lp+fods + the additional language pack+fods, it took quite a bit of work but i have it running smoothly now, i'll implement it in my lab over the next day or so and blog it.
-
i'll blog it as soon as i can then you'll have the info
-
I've done it (via a task sequence), and have it working perfectly both for language packs and the associated keyboard settings, I was planning on blogging it, thanks for reminding me
-
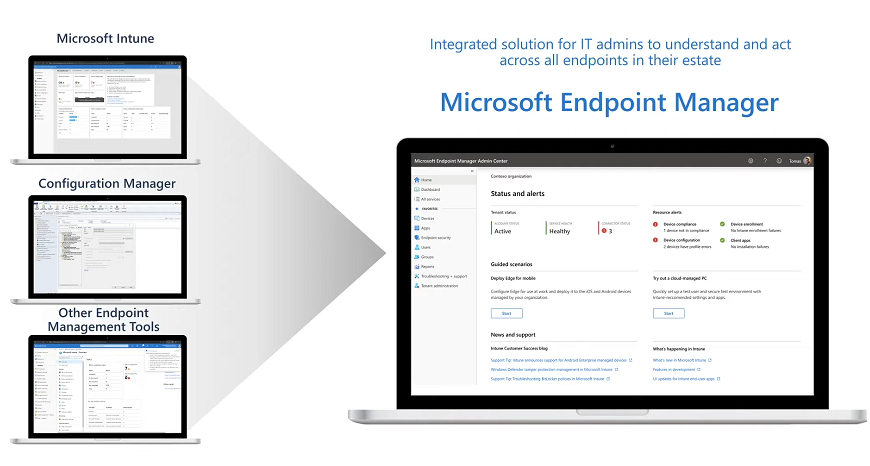
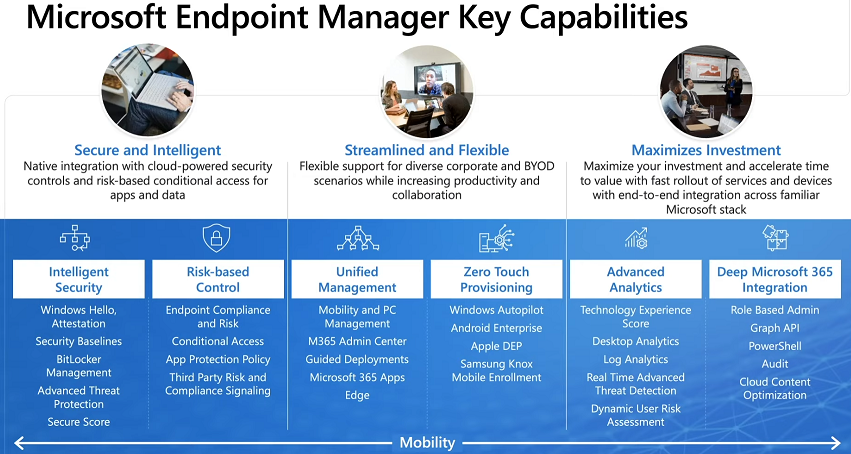
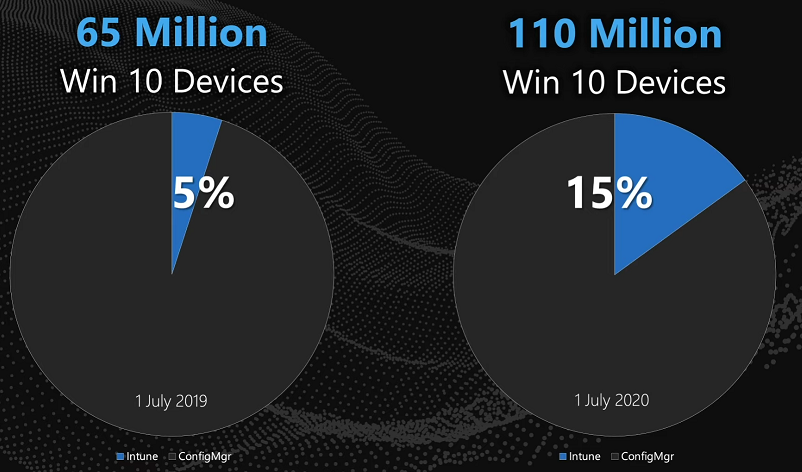
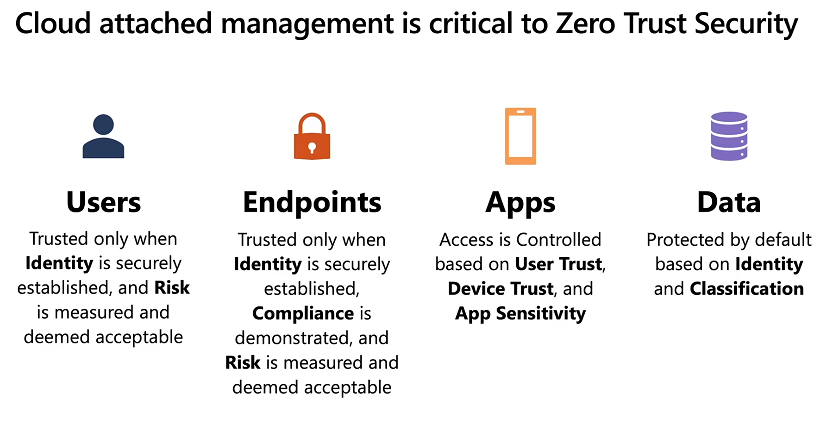
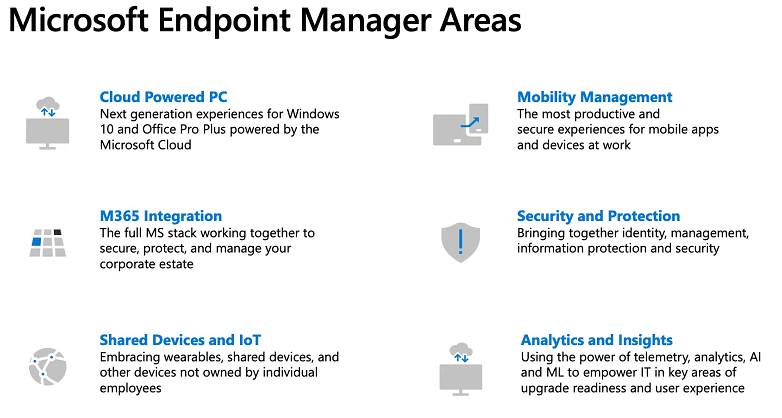
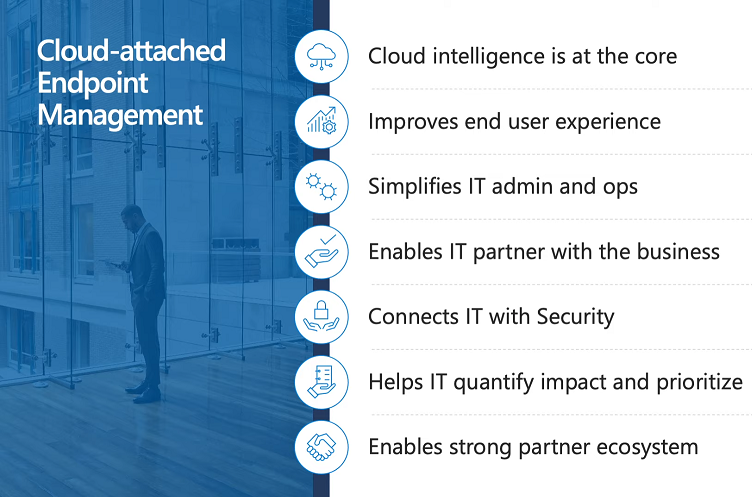
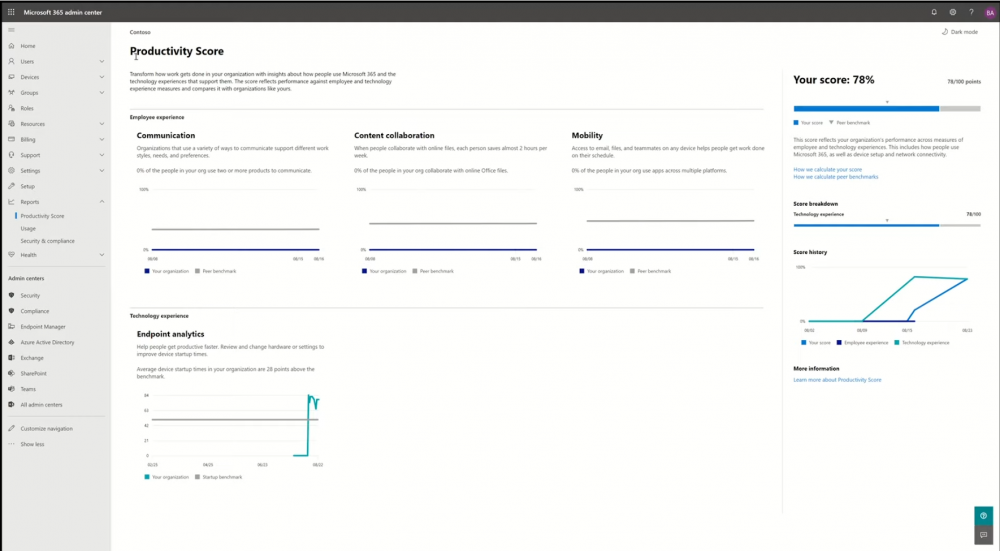
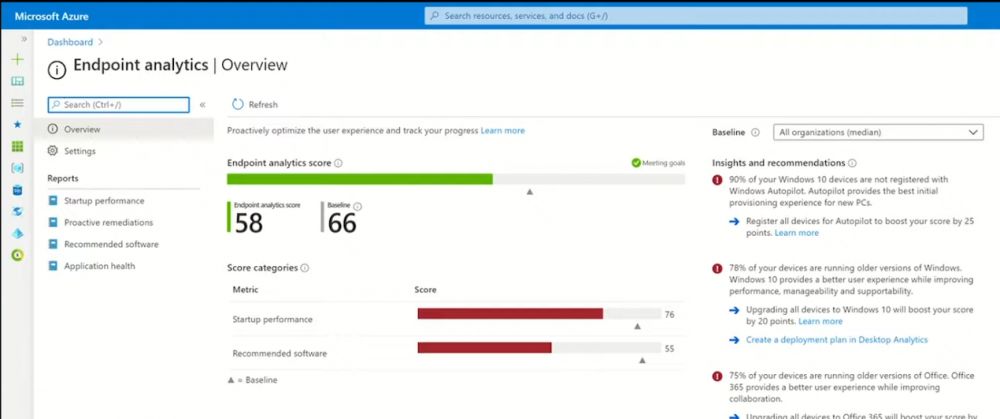
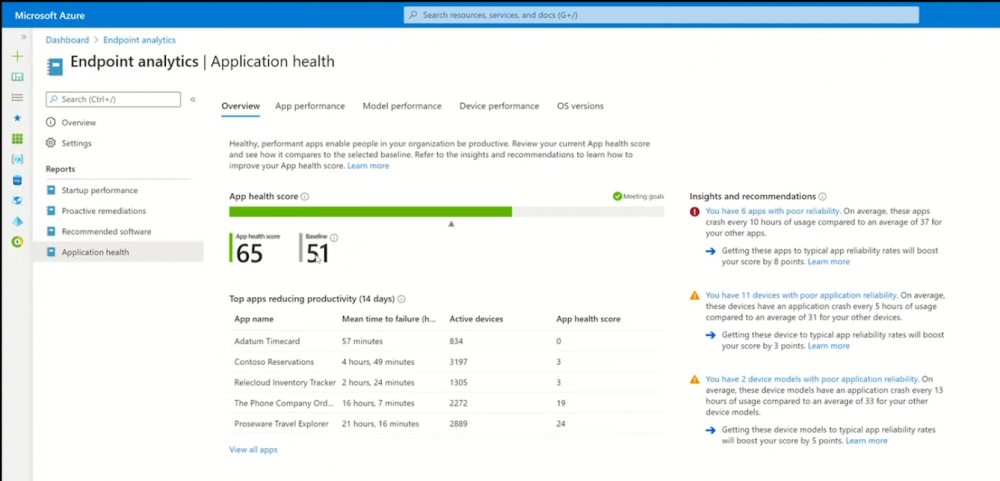
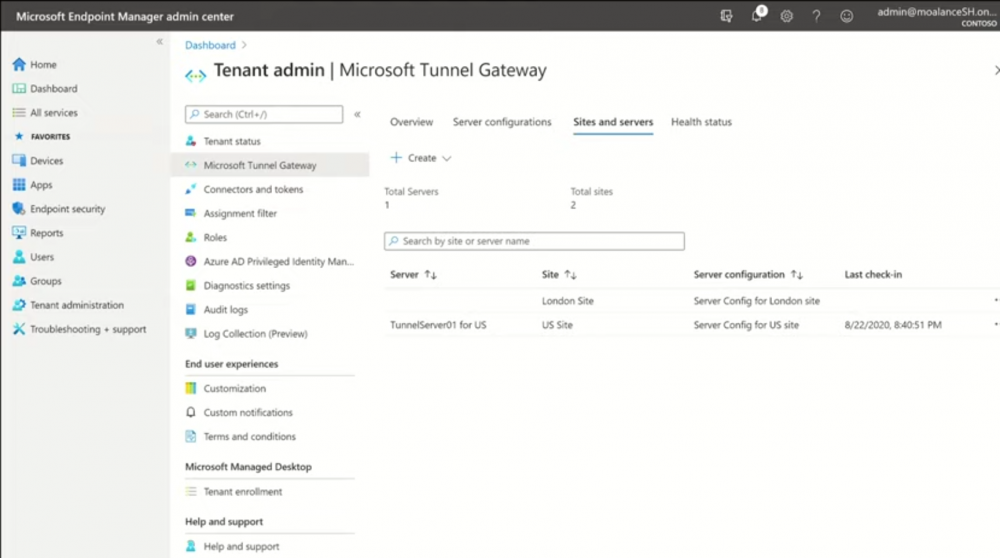
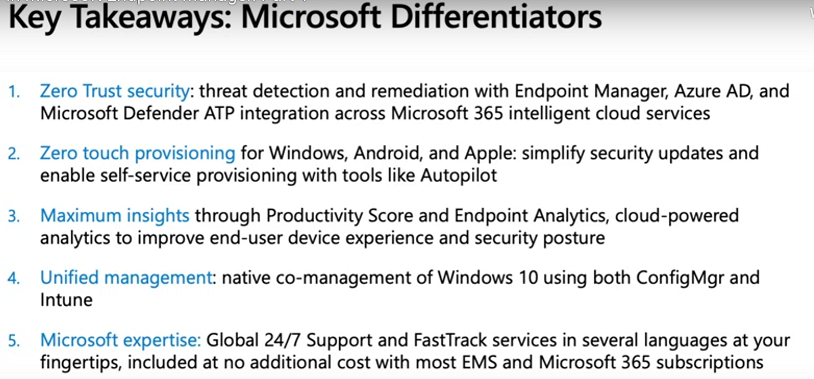
Introduction These are my notes from a session shown today @ Microsoft Ignite 2020, the session was hosted by Steve Dispensa (Director of Program Management at Microsoft Endpoint Manager) and Ramya Chitrakar (Director of Engineering at Microsoft Endpoint Manager). For the last couple of years at Ignite I blog my notes for sessions I'm interested in as I always find it nice to later refer to this reading material and punctuate it with content I've covered, and sometimes the videos just flow by too fast and you miss out on important points. Where appropriate I'll link to content that I've covered that is referred to in the video. This is part 1 of a two part series: What's new in Microsoft Endpoint Manager - part 1 (this part) What's new in Microsoft Endpoint Manager - part 2 Agenda MEM and the new normal What's new in Microsoft Endpoint Manager Demos Takeaways and next steps MEM and the new normal A year ago we all started our day in the usual way, grabbing coffee, going to the office, and interacting directly with our fellow colleagues but Covid 19 changed that very quickly as businesses shut their doors all around the world. I know this myself as I've been working from home since mid-March this year and as a direct result of that I upgraded my home office to make the work environment more appealing. Now many of us are working from home either full time or most of the time, and that involves changes in how we access and use company resources. We are working across more devices, more scenarios and often without the traditional safety net of onsite support or help desks that you can visit directly for assistance. This rapid change has guaranteed one thing, all businesses must have a remote working plan that lets employees work with 100% productivity from home. "Businesses need users to be fully effective when working remotely and need to be able to switch between remote work and office work without missing a beat" Last year at Ignite Microsoft released Microsoft Endpoint Manager, the integrated solution between all the endpoints in your estate. MEM brings together Intune (intelligent cloud) for all of your cloud attached endpoints, Configuration Manager (Intelligent Edge) for all your on-premises endpoints and other endpoint management tools suchs as Windows Autopilot, Desktop Analytics and Proactive Remediations to bring the power of the cloud to your whole enterprise. Microsoft have seen exponential growth in cloud attachment in the last year. "Massive customer adoption" MEM brings together the most comprehensive set of endpoint management capabilities in the industry. Starting with security it integrates with the most sophisticated solutions in the market and lets you establish baselines and implement policy for your users and devices. Risk based controls like Conditional Access lets you make sure that your endpoints are secure and compliant before gaining access to sensitive company resources. Unified management has deep integration with Microsoft 365 apps and the new Microsoft Edge. Zero touch provisioning works across different platforms to deliver unprecedented efficiency for IT Pros. And of course there is advanced analytics with Desktop Analytics, Log Analytics, real time advanced threat detection and more, and of course it's all deeply integrated with Microsoft 365 and can utilize RBAC (role based access control), Microsoft Graph (to automate tasks), PowerShell, auditing and cloud content optimization. So how does it all fit together ? "Tenant attach" Microsoft's goal is to bring the power of the cloud to your whole enterprise. Microsoft released tenant attach which allows you to have an easy and low risk path to cloud attached Configuration Manager to start gaining cloud benefits. I blogged about tenant attach when it was first released in Endpoint Manager technical preview below: Enabling tenant attach Utilizing tenant attach Organizations can also use co-management to manage Windows 10 using both Config Manager and Intune at the same time, this capability is unique in the industry. New customers can go directly to the cloud with Intune or migrate over time with co-management of Config Manager and Intune. Below you can see the increase in numbers of Windows 10 devices managed in the cloud (Intune) in the last year. The target for next year is 35% managed by Intune and by 2022 they are forecasting 50% of Windows 10 devices will be cloud attached. Nobody had it easy through this crisis, but customers that had modern management definitely had a smoother run. The pandemic drove permanent changes in the way modern workplaces worked, customers deployed CMG's, VPN usage went crazy. At this point however most customers have made it through the initial problems and are focusing on rebuilding for the future. So let's focus on the new capabilities in Microsoft Endpoint Manager. What's new MEM will support virtual endpoints so you can support Windows Virtual Desktop and later this year, third party VDI right alongside your physical pc's. They will preview this capability later in the year. Customers want to manage all their endpoints with MEM and Microsoft have a first class management experience of MacOS. New capabilities there as well including the ability to deploy scripts to devices, new enrollment experiences that utilize Single Sign-on improvements across applications and new managed life-cycle features. Shared iPad for Business support. Will let customers deploy shared iPads to users, login with their Azure AD work accounts in separate partitions on the device including having each user having a separate device passcode on the device. Introducing Microsoft Tunnel. Customers have been asking for this literally for years. Tunnel allows you to connect your users on iOS and Android to apps and services. Full device and per app VPN with split tunneling. Natively integrated with Microsoft 365 and Conditional Access so you can protect your sensitive company resources. This is now available in preview to a broad audience over the next couple of days. Please check it out. "Zero Trust" Cloud attached management is critical to Zero Trust Security and Endpoints are trusted only when identity is securely established. MEM si growing fast, and it also offers the following areas of investment in new classes of shared devices. Today Microsoft will announce the general availability of Endpoint Analytics which is one of the fastest growing new capabilities in MEM. Every cloud attachment is unique and there are several different on-ramps to cloud management and (according to Microsoft) it's just a couple of clicks, but in reality you do have to satisfy prerequisites and those take some time to setup prior to those clicks. Demos As Steve already mentioned there's been a massive shift towards remote work and a strong indication that this trend will continue even in the long term. Ensuring business continuity and resilience is going to be key for IT. Microsoft Productivity score and Endpoint Analytics enable the IT Pro to understand how organizations are working, how technology is supporting them and how productive their end users are. "Microsoft Productivity score and Endpoint Analytics enable the IT Pro to understand how organizations are working, how technology is supporting them and how productive their end users are." Analytics really makes the IT Pro the hero. Endpoint Analytics is release to general availability at Ignite, Microsoft Productivity Score will be released in October. Below you can see the productivity score and how it displays employee experience and technology experience. Endpoint analytics is part of Technology experience, last year Microsoft announced some cool new features in that area to measure startup performance. It also offers Proactive remediations, recommended software and application health reports. Application health (new) is based on the 0-100 paradigm. Shows you top applications that affect your performance over the last 14 days. Overlays crash data over the usage of each app and the number of devices that are using this app. This let's you focus on the top applications that are impacting productivity. Conditional access Conditional access enables zero trust access control where identity is the parameter and all endpoints are treated equally regardless of the network that they attach to. Customers are telling Microsoft that they have some legacy applications that are simply not ready for modern authentication and conditional access. "Microsoft Tunnel is a mobile access gateway. Microsoft Tunnel is a vpn gateway to allow your iOS and Android users to access apps and on premise resources using modern authentication, single sign-on (sso) and conditional access." Microsoft Tunnel is a mobile access gateway to take care of this. Microsoft Tunnel is a vpn gateway to allow your iOS and Android users to access apps and on premise resources using modern authentication, single sign-on (sso) and conditional access. This is setup by the IT admin. There are three main steps. Configure the gateway Deploy VPN profile for Tunnel Deploy Edge and Tunnel apps for these devices You can find this new functionality under Tenant Administration in the Endpoint Manager console. Key takeaways Recommended reading Working from home - the new reality Introducing Microsoft Tunnel Microsoft Productivity Score https://adoption.microsoft.com/productivity-score/ Endpoint Analytics https://docs.microsoft.com/en-us/mem/analytics/overview Microsoft Endpoint Manager https://endpoint.microsoft.com
-
ok i've connected to your lab just now and fixed the internal issues, basically to summarize your internal lab was not following my lab setup, and you had DNS configured incorrectly, so your srv0001 server (dc01) was 192.168.3.1 or something, when it should have been 192.168.11.101 and so on, so when i pinged from the sccm server to the dc it replied back with 192.168.3.1 (or whatever ip it was, i forget), in addition, your webserver had ip address of 192.168.11.100 so it was not going to work, ive fixed dns by deleting the stale entries, and manually configuring the ip on the dc and on the sccm server and lastly disabled ipv6 on all 3 servers, rebooted them, and verified all could ping each other, that's the first thing you need to have working before trying anything else, don't reuse labs from something else, they will break, always build labs from scratch as per the offered guide, then it will work 100% lastly, i confirmed that your smoothwall was configured correctly, it looked ok, then i checked port 80 on your internet ip address with canyouseeme.org and it didn't work, that means that more than likely your internet provider or router/adsl/whatever is blocking port 80, so please check that
-
hi there worst case scenario while you are troubleshooting the problem you can create bootable media in ConfigMgr, to boot the laptops (usb or cd) and then image them as normal. But as regards your problem, are you sure that the task sequence deployed contains the new boot image ? and it's distributed to all dp's ?
-
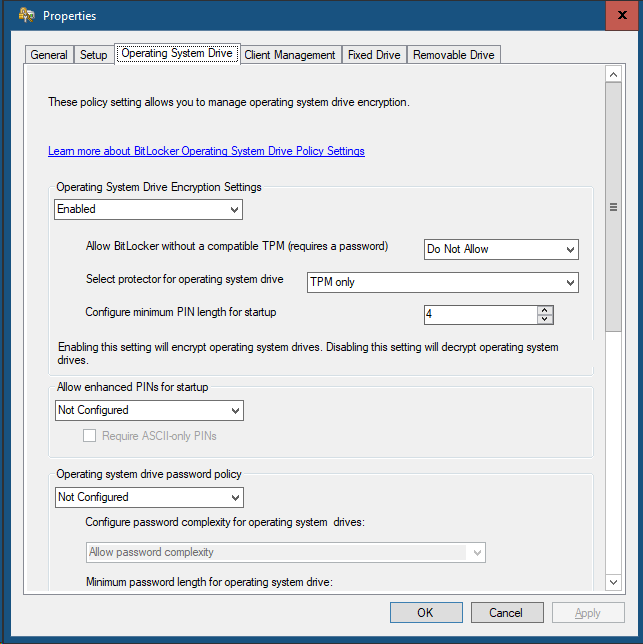
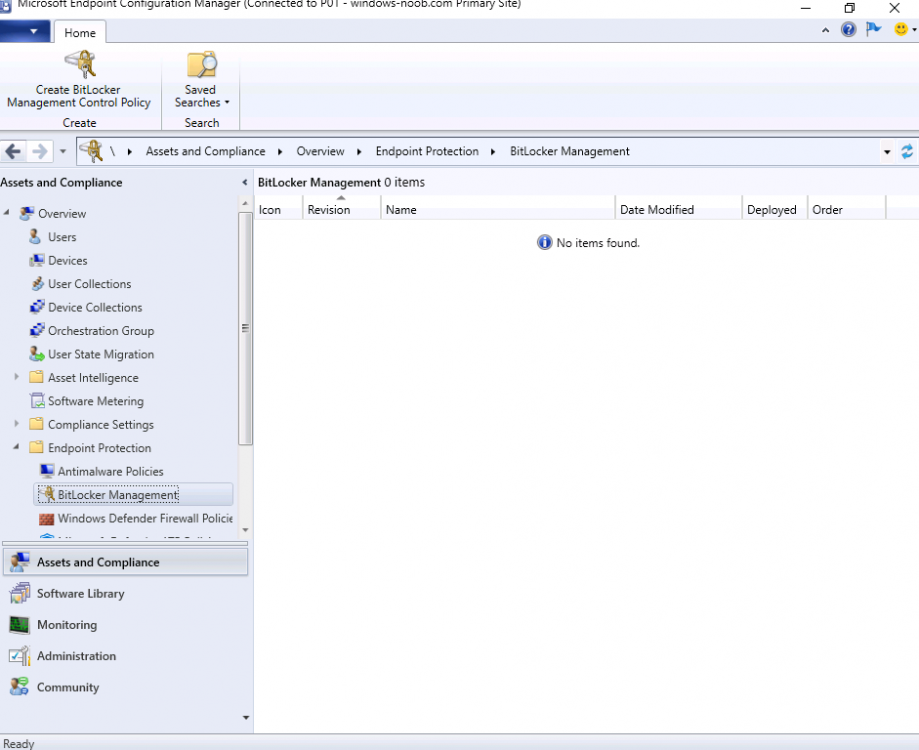
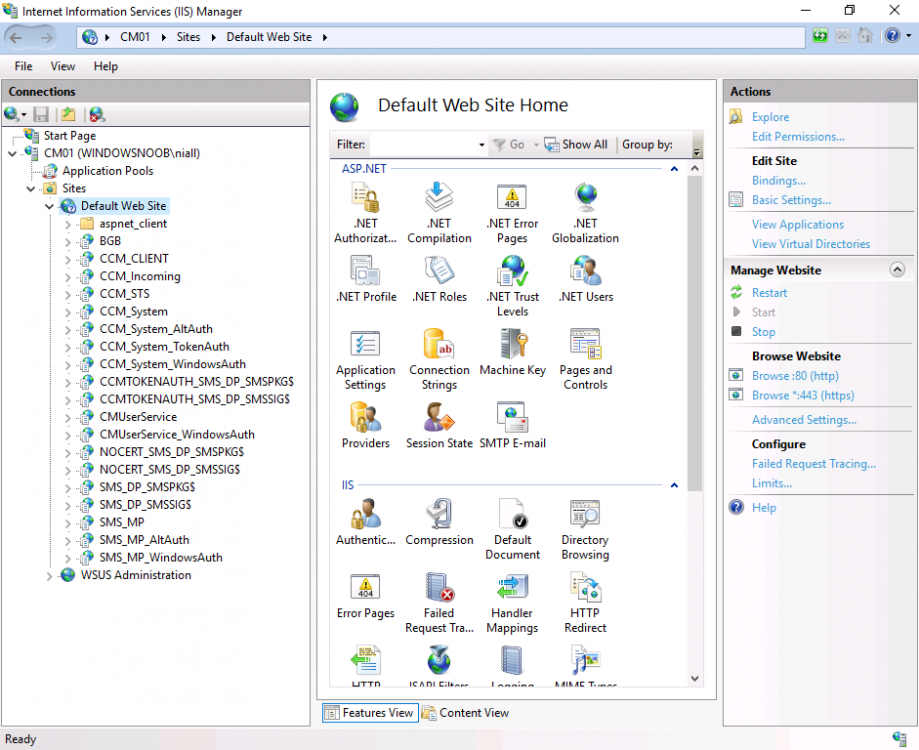
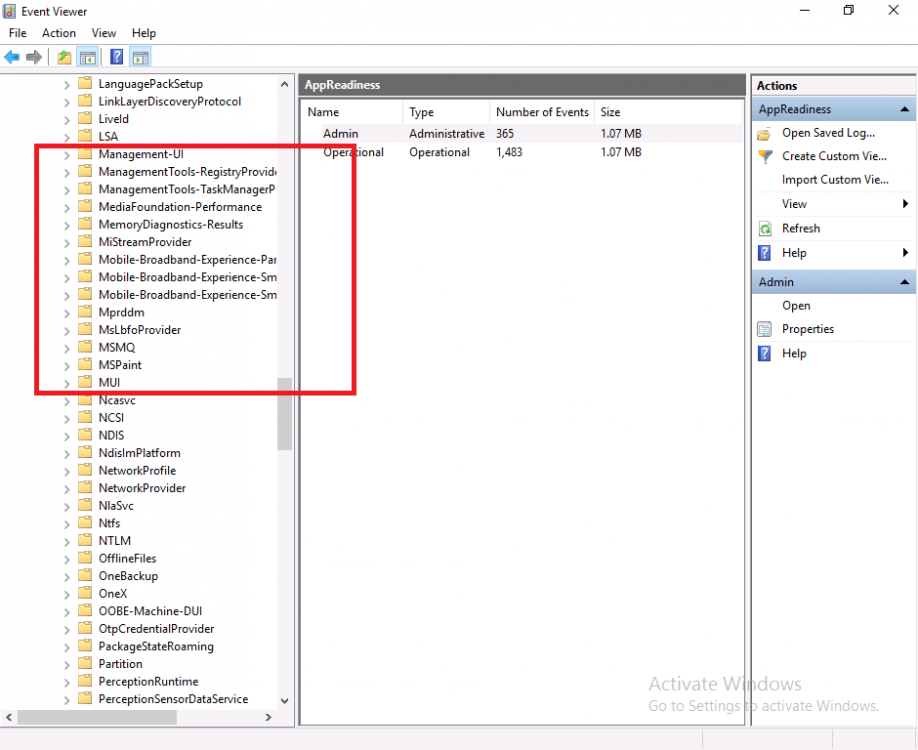
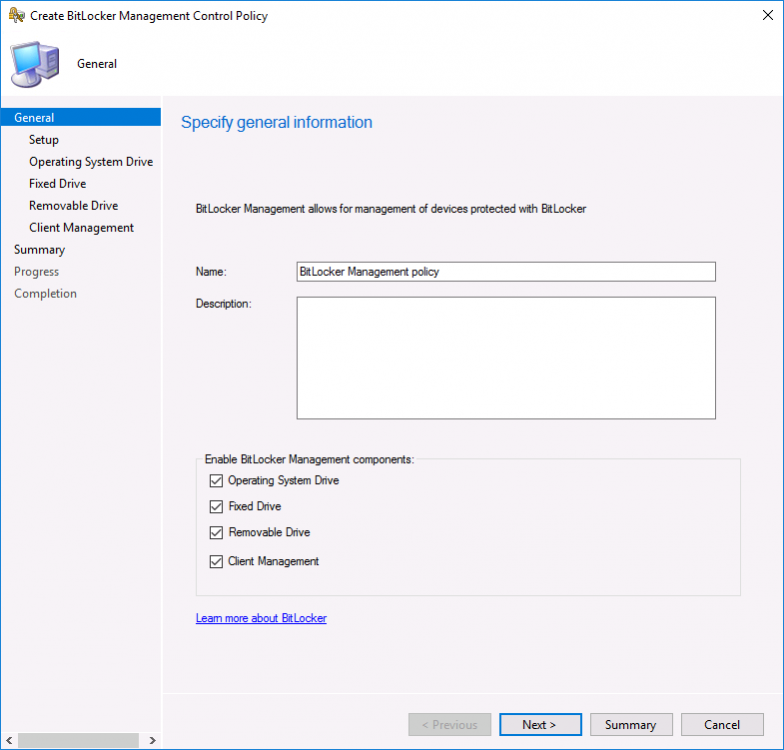
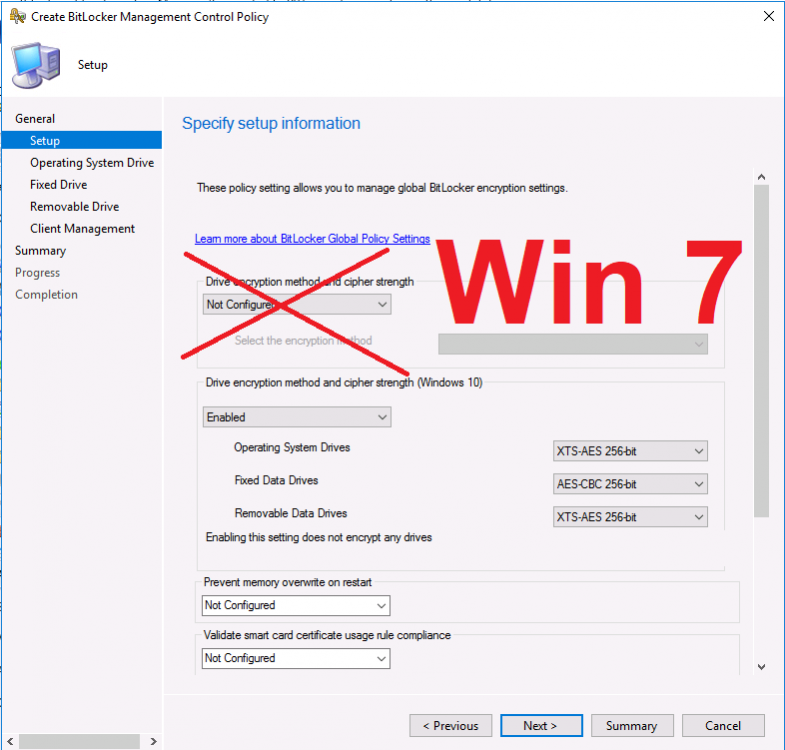
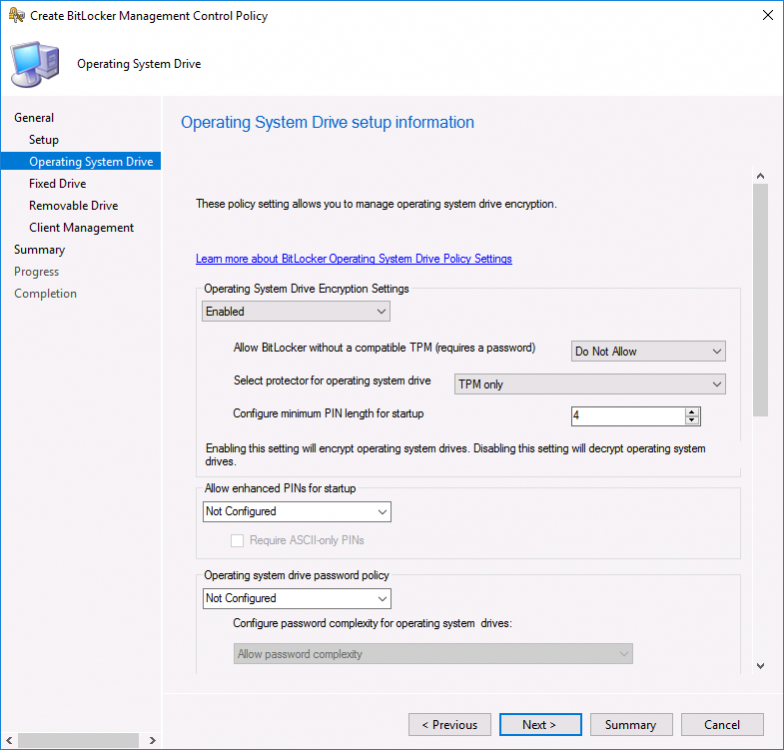
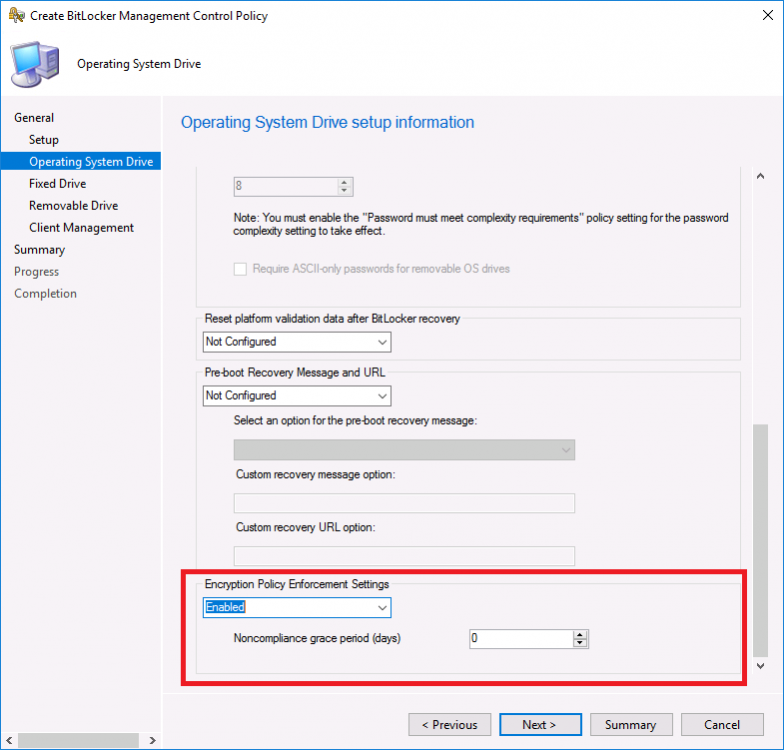
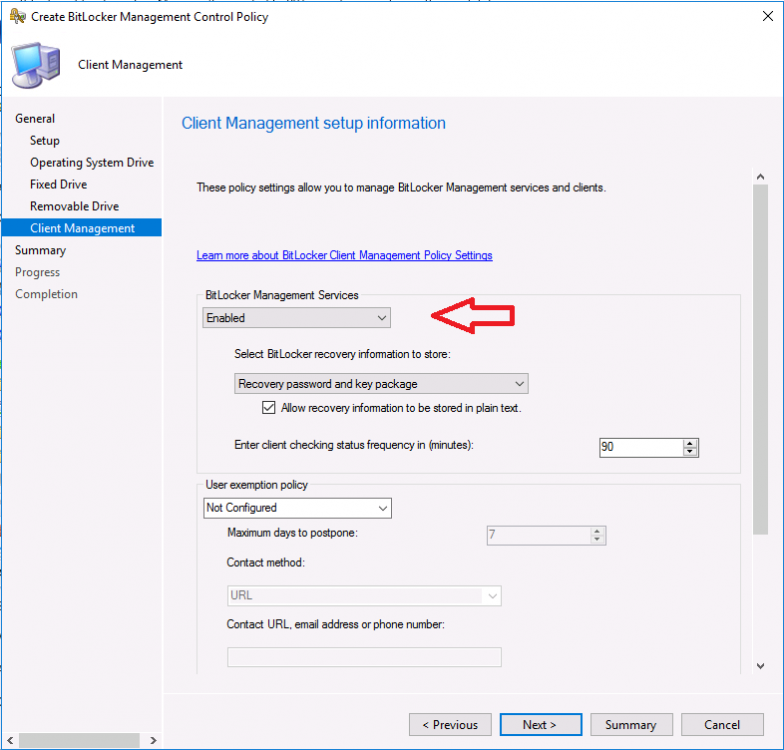
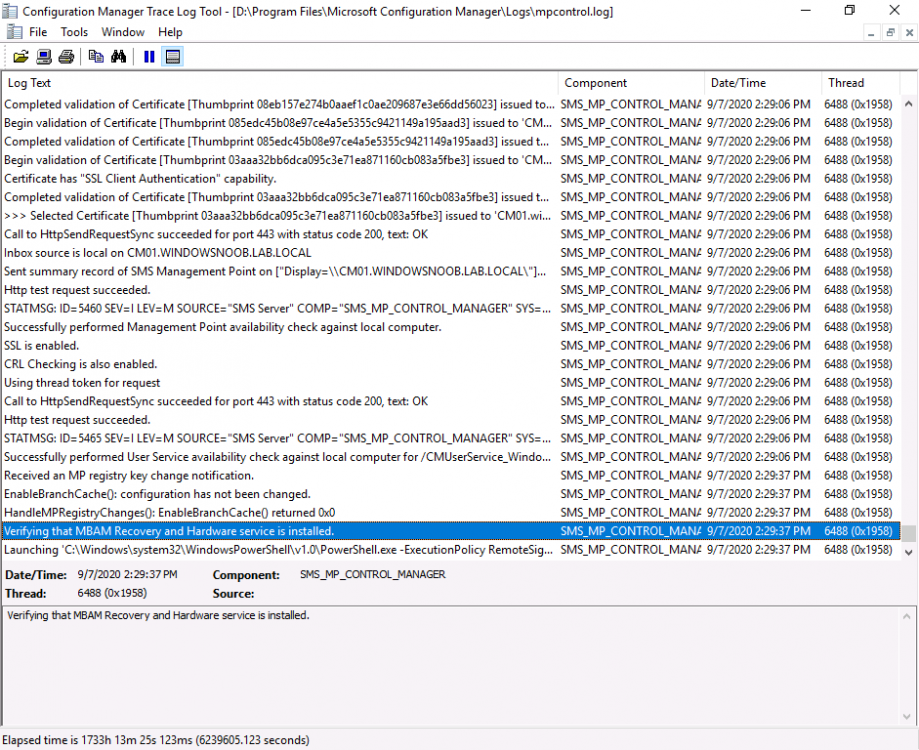
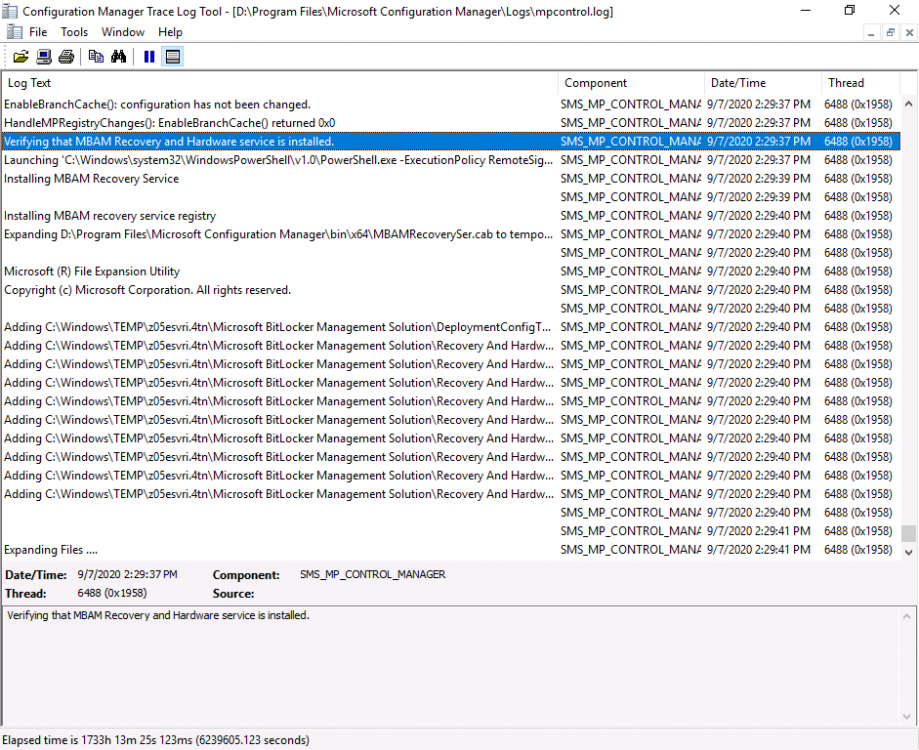
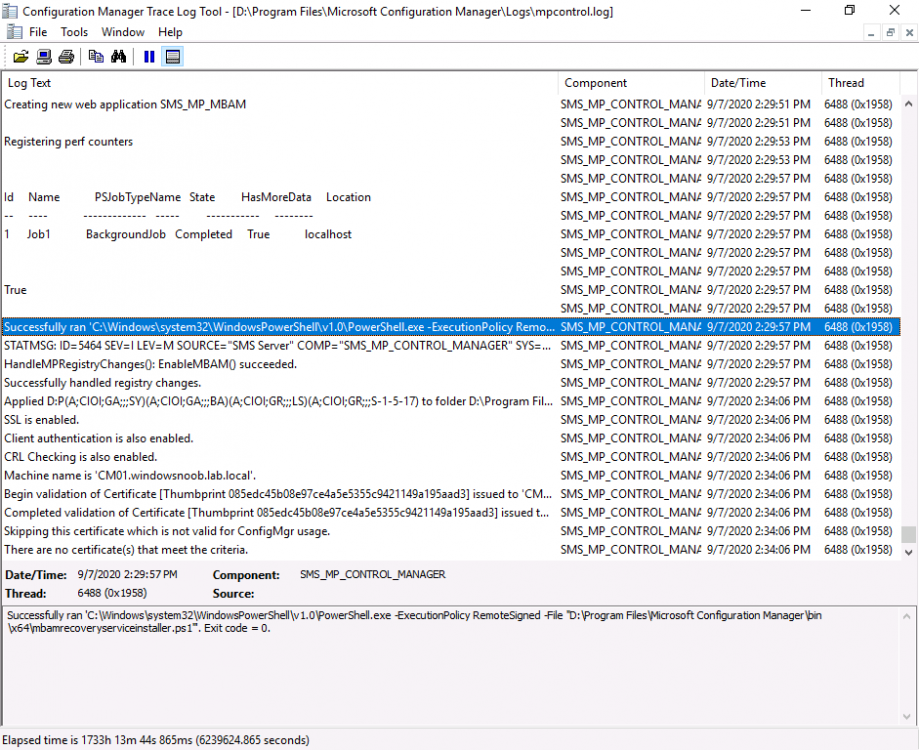
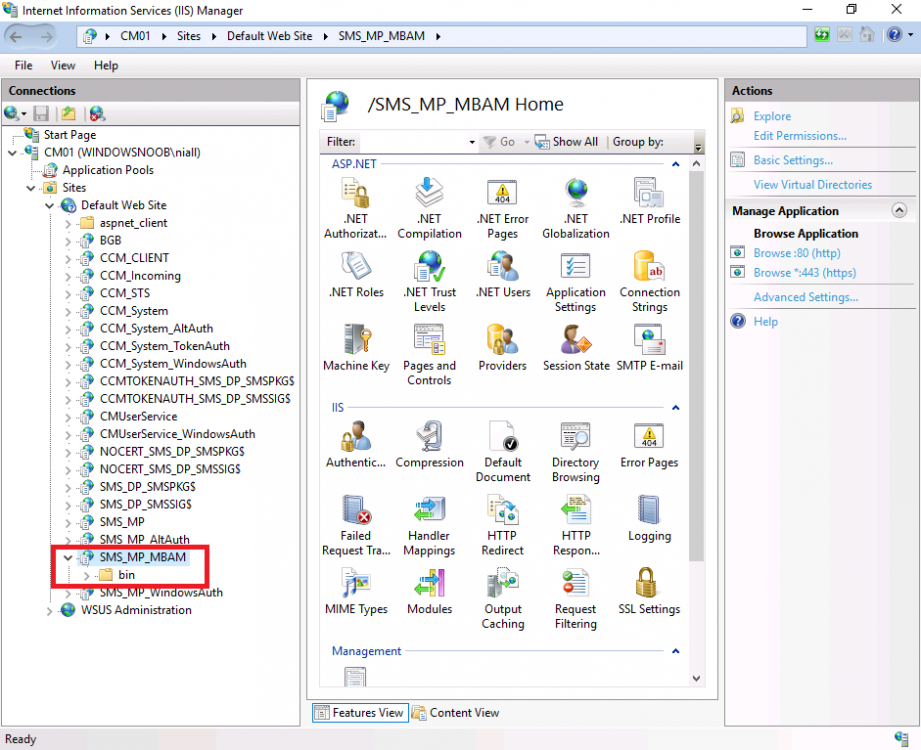
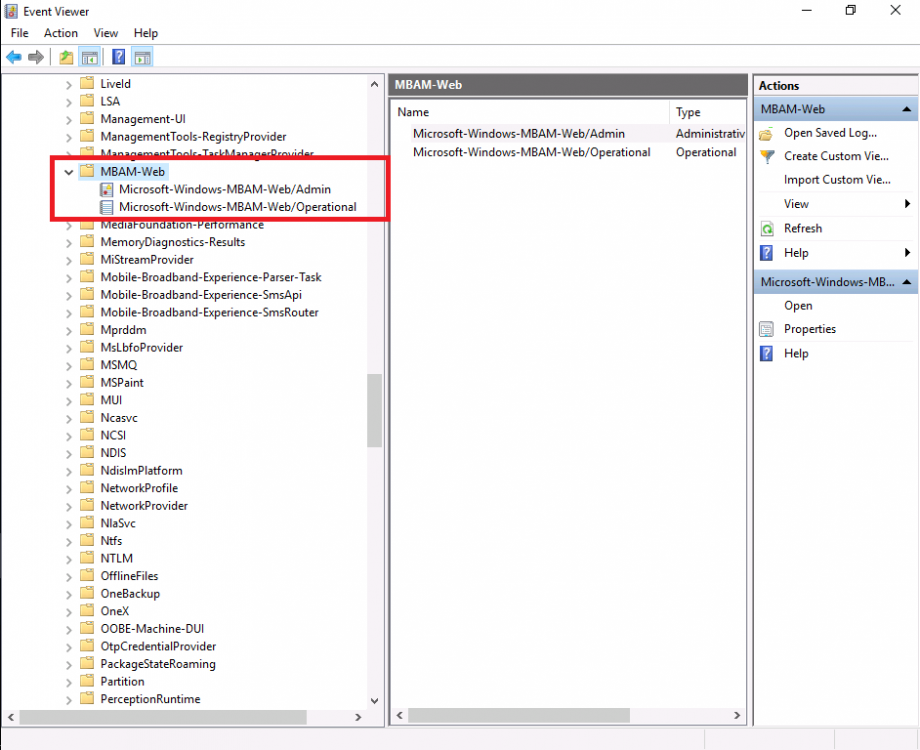
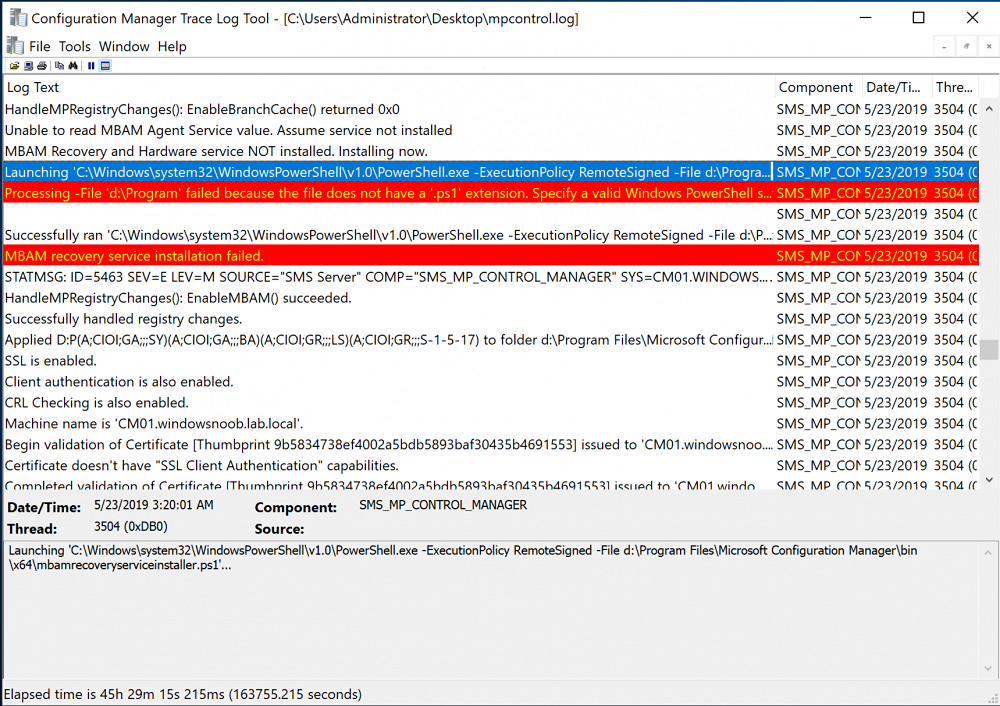
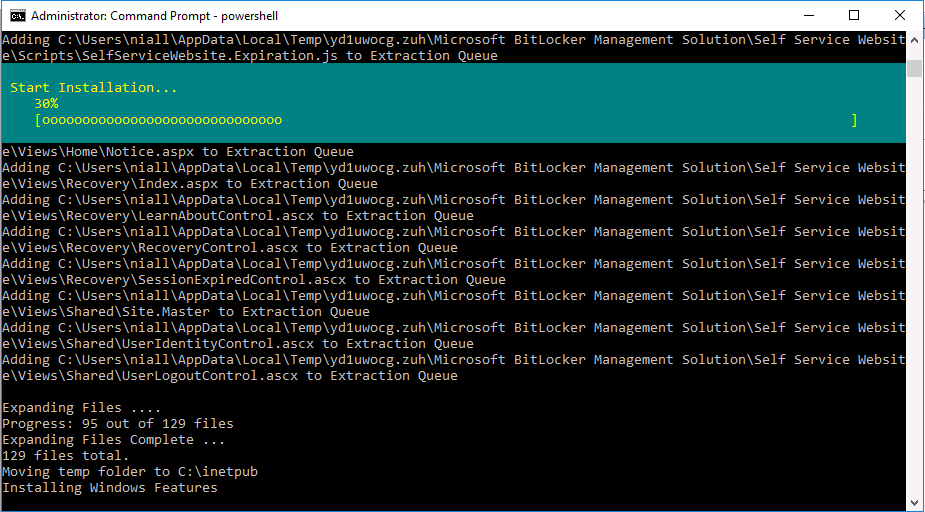
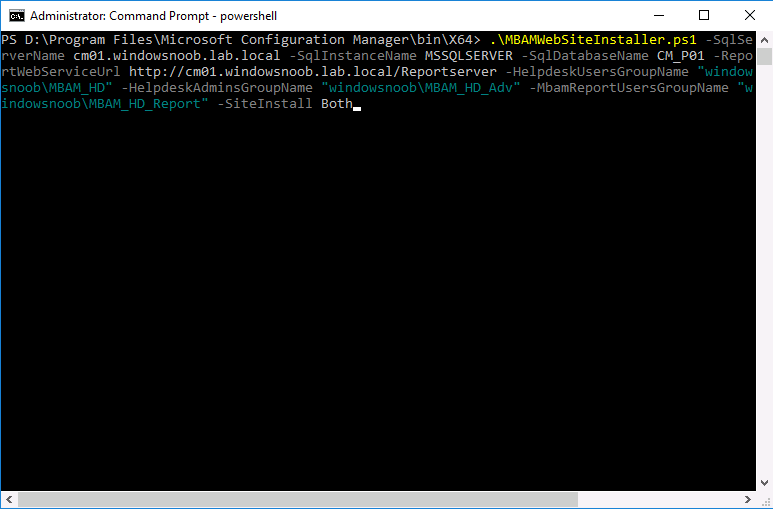
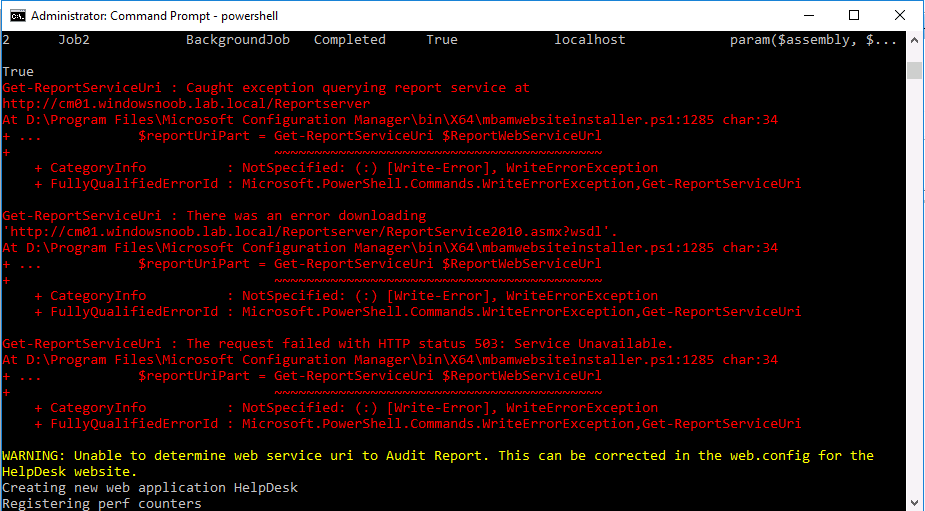
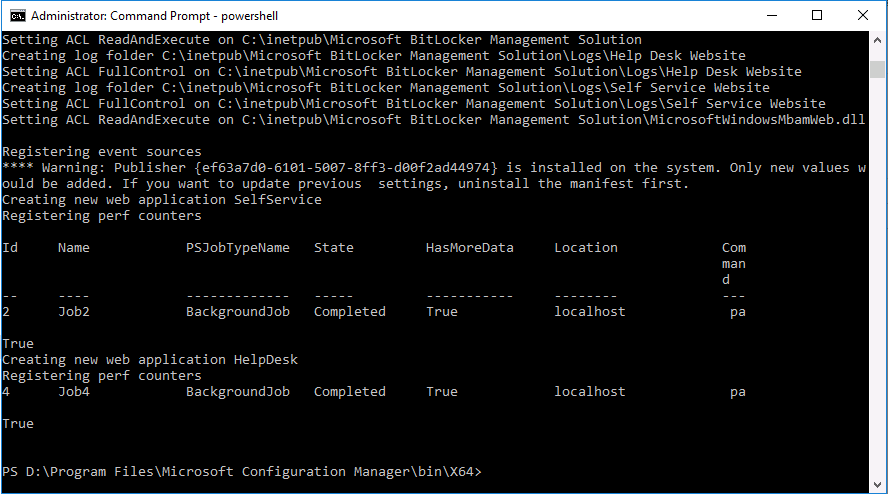
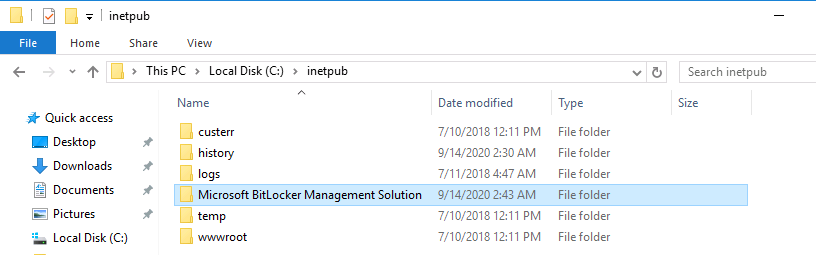
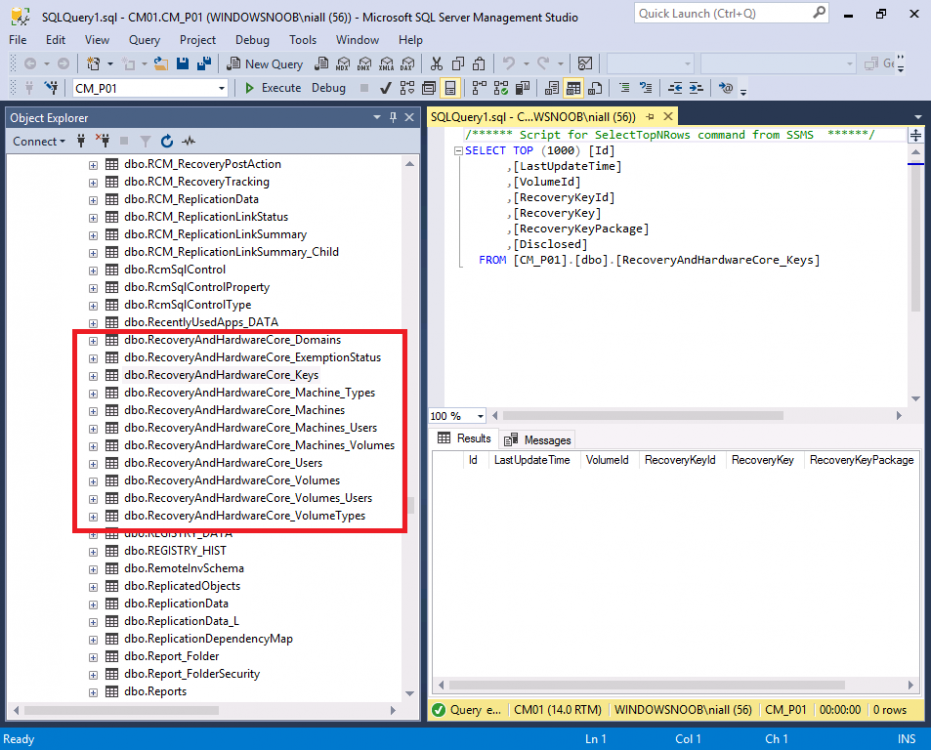
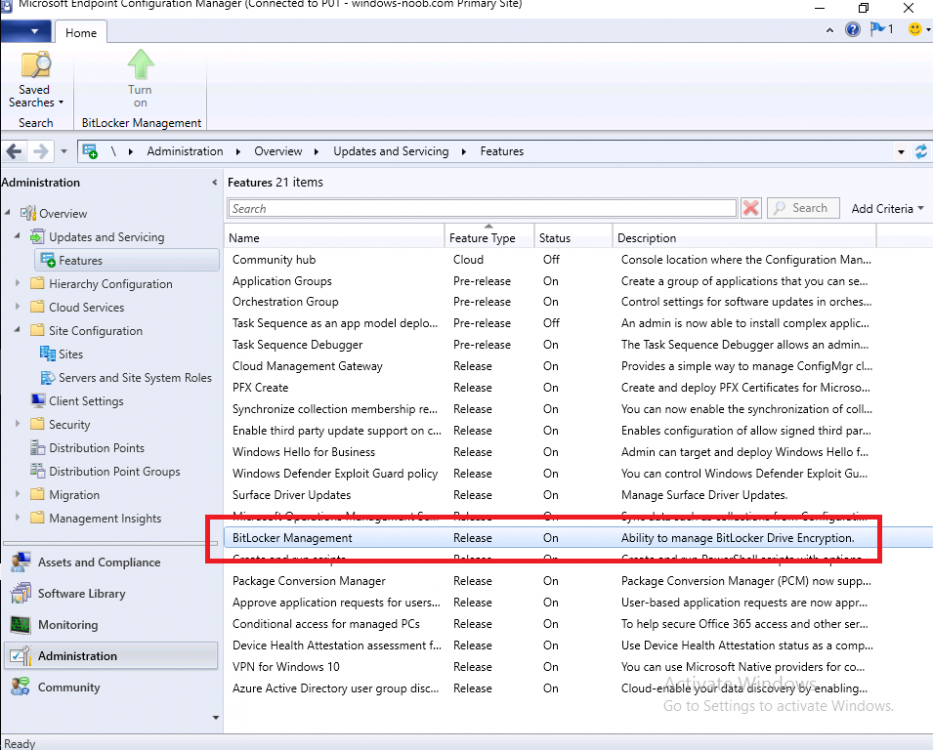
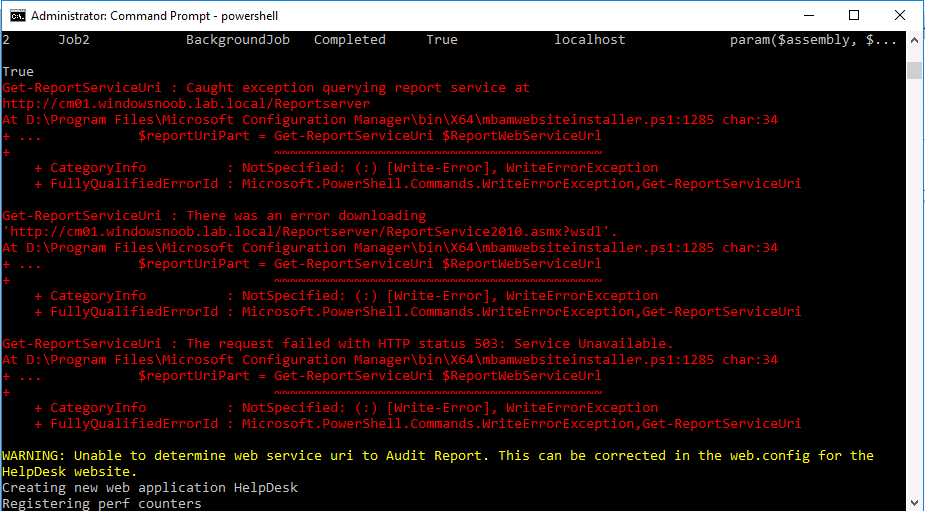
Introduction Microsoft blogged about Bitlocker Management capabilities back in May, 2019. They detailed how that would impact and evolve on the following three platforms. Cloud-based BitLocker management using Microsoft Intune On-premises BitLocker management using System Center Configuration Manager Microsoft BitLocker Administration and Monitoring (MBAM) And recently they've posted an updated blog post here where they go into detail about how BitLocker Management in Microsoft Endpoint Manager has evolved (both in Intune and ConfigMgr). This purpose of this mini series is to help you troubleshoot problems related to the installation, configuration and usage of the new BitLocker Management capabilities in ConfigMgr and will be broken down into the following 3 parts. Troubleshooting BitLocker Management in ConfigMgr - Part 1. Server side (this part) Troubleshooting BitLocker Management in ConfigMgr - Part 2. Client side Troubleshooting BitLocker Management in ConfigMgr - Part 3. Common issues But first let's take a quick trip down memory lane. Microsoft initially released Bitlocker Management capabilities in the 1905 version (Technical Preview) of Configuration Manager, and expanded upon the abilities up to the release of the BitLocker Management feature contained within Configuration Manager version 1910 (Current Branch). After 1910 was released they have continued to improve and add new features as you can see by checking out any of the newer Technical Preview releases from Technical Preview version 2002 on wards where many GPO settings were added to the Bitlocker management UI. In addition new capabilities came in TP2005 (set BitLocker Encryption type during the Enable BitLocker and Pre-Provision BitLocker steps in an OSD task sequence that later made their way into Configuration Manager Current Branch version 2006, so it pays to look at the technical preview releases every month. Note: The screenshot below is taken from Technical Preview version 2008 I have created many blog posts and videos on the subject, so if you are interested then please take a look at the videos linked below. Installation and troubleshooting on the server When you use the BitLocker Management feature in ConfigMgr 1910 or later you can create BitLocker Management policy and deploy that to your clients, they will get the policy and process it, and the MDOP client agent will get installed (if not already installed) and then it will take action based on the settings it finds in the registry and based on the policy settings and the client settings compliance will be set. But, it's important to understand the flow of how it all works together and to do that you need to understand that things will change based on whether you've created BitLocker Management policy or not. In this post I assume you've met the prereqs and enabled the BitLocker Management feature as shown here. Before creating policy First of all, let's look at a ConfigMgr 2002 Current Branch server where no BitLocker Policy has yet been created. You can think of this as a server that has been recently upgraded from 1910 or one where no one has configured anything related to Bitlocker Management yet. In this blog post the primary server in my lab is not using co-Management but if it was, you'd need to ensure that the Endpoint Protection workload was managed by ConfigMgr if you want ConfigMgr to manage BitLocker Management. The Configuration Manager client handler for BitLocker is co-management aware. If the device is co-managed, and you switch the Endpoint Protection workload to Intune, then the Configuration Manager client ignores its BitLocker policy. The device gets Windows encryption policy from Intune. When you switch encryption management authorities and the desired encryption algorithm also changes, you will need to plan for re-encryption . In the console, expand Endpoint Protection in Assets and Compliance and you'll see BitLocker Management. Select it, there will be no items found as no policy has yet been created. In addition, if you open Internet Information Services (IIS) Manager, you will not see any MBAM related applications in there. and there will be no MBAM related logs in Windows Event Viewer After creating policy When you create your first BitLocker Management policy you'll see MBAM related activity revealed in the mpcontrol.log on the ConfigMgr server. This is your first step to look in case of problems on your server. So let's create our first BitLocker Management policy. On the setup window, don't select the first option, it's only applicable to old operating systems such as Windows 7 and that's not supported any more. Instead, use the drop down underneath that for Windows 10. Configure your Operating System drive settings. And decide what Encryption enforcement you require. Setting it to zero will mean that the MDOP agent will not notify the end user and instead, will begin encryption silently (as long as everything is configured correctly and the client is not already encrypted). Don't forget to enable Client Management otherwise the registry keys necessary for the recovery service will never get populated on the client and as a result, BitLocker Management will not work. After creating policy After you've created the policy, open mpcontrol.log and look for a line which reads Verify that MBAM Recovery and Hardware service is installed. shortly after that it starts installing the MBAM Recovery Service And you should confirm that the PowerShell script (mbamrecoveryserviceinstaller.ps1) used to install the MBAM Recovery Service successfully completed. To see what a failed MBAM Recovery service installation looks like take a look at the mpcontrol.log below from an older lab. This is just for comparison purposes, notice how it states MBAM recovery service installation failed. After the script has run successfully, you can refresh Internet Information Services (IIS) Manager, and you should see the SMS_MP_MBAM application is now listed. In addition, in Event Viewer, you will now see MBAM specific logging areas added. These will populate with info if there are problems detected on your MBAM Recovery Service. Installation of the web portals The BitLocker Management web portals (helpdesk and self service) may or may not be installed on the same site server as the MBAM Recovery Service, in my lab, they will be installed on the same server (ConfigMgr Primary site). To install the portals you need to run a PowerShell script included with ConfigMgr version 1910 or later, it's in the bin\x64 folder of the installation source. Below is the command line I used to install the portals on my Primary. After pressing enter, it start's copying files, settings acl's and so forth. However mine bombed out with some red errors which hinted towards the problem being SSRS reporting related. This could be trued if you either have not installed or configured SSRS or SSRS itself has a problem. After some troubleshooting I determined that my SSRS instance had expired (it was evaluation media), so I fixed it by doing as follows. After resolving the SSRS issue, the web portals installed just fine. You can scroll back up to see all the text output to see if there was any problem reported. If you'd like to compare my successful output with yours then you can download the output here.web portals setup text.txt After you have successfully installed the web portals, you can browse to the InetPub root folder on your ConfigMgr server, and you'll see a new folder called Microsoft BitLocker Management Solution. This folder did not exist until you attempted to install the web portals. That folder in turn contains more folders, which have config files that can be edited as described in the blogs below. How can you use the Self Service feature when BitLocker Management is enabled within ConfigMgr ? How can you use the Help Desk feature when BitLocker Management is enabled within ConfigMgr ? What about log traces ? If you need to enable tracing on the server, use the SvcTraceViewer.exe tool to review those traces as described here. What about the database ? After successfully creating BitLocker Management policy, you'll notice new tables are present in ConfigMgr's database. Below you can see them in my lab, note that they are not yet populated as it's a new installation. Obviously if those tables are not present then you have a big problem. That's if for this part, join me in Part 2 where we'll look at the Client side troubleshooting. Recommended reading https://www.niallbrady.com/2019/11/13/want-to-learn-about-the-new-bitlocker-management-in-microsoft-endpoint-manager-configuration-manager/ Until next time, adios ! cheers niall
-
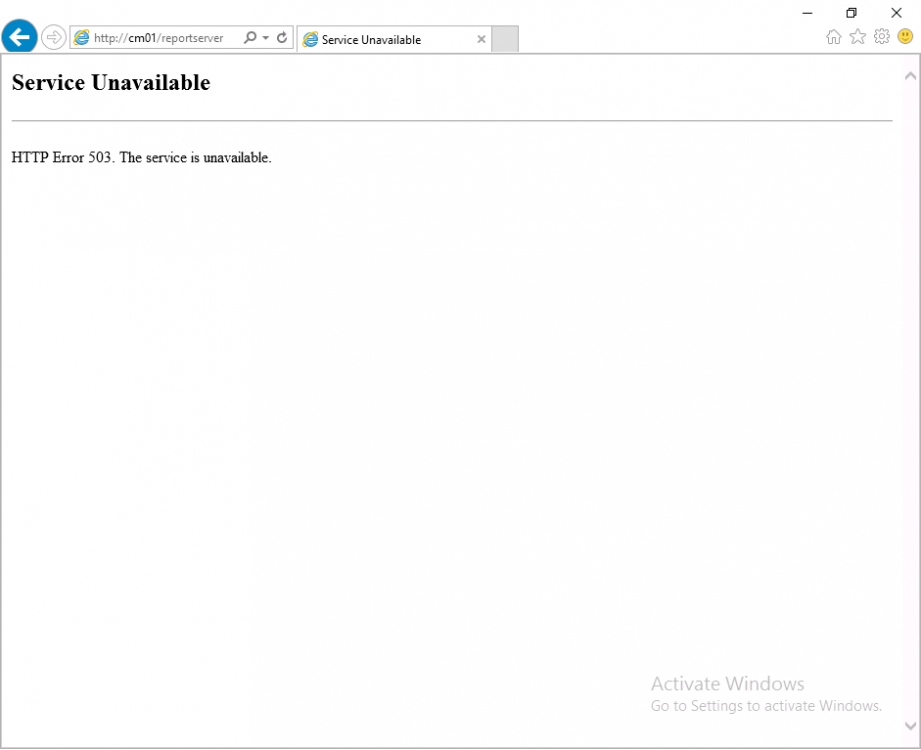
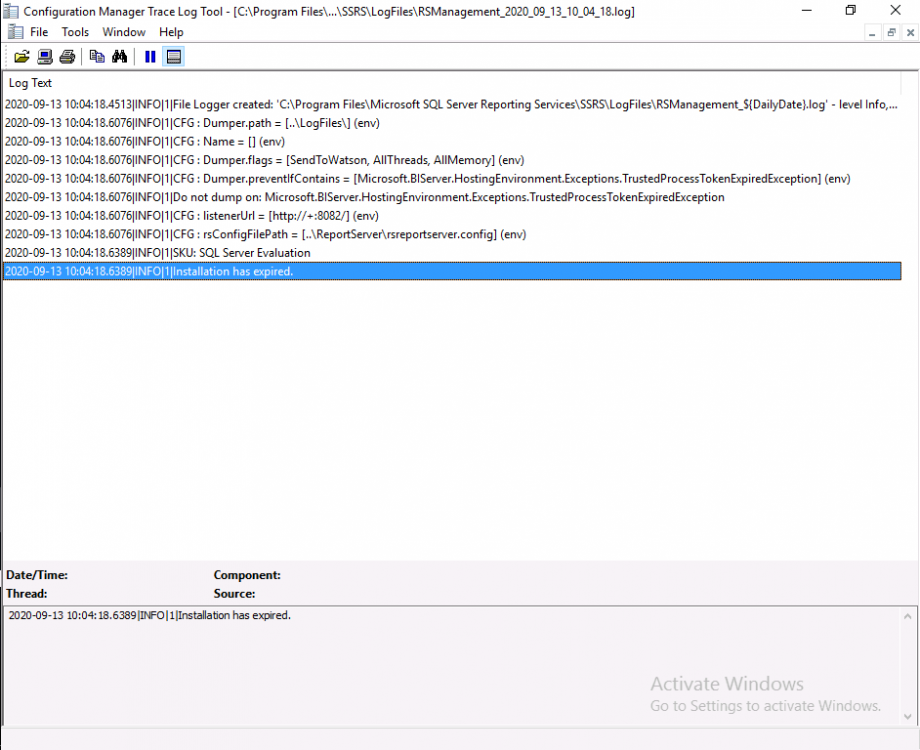
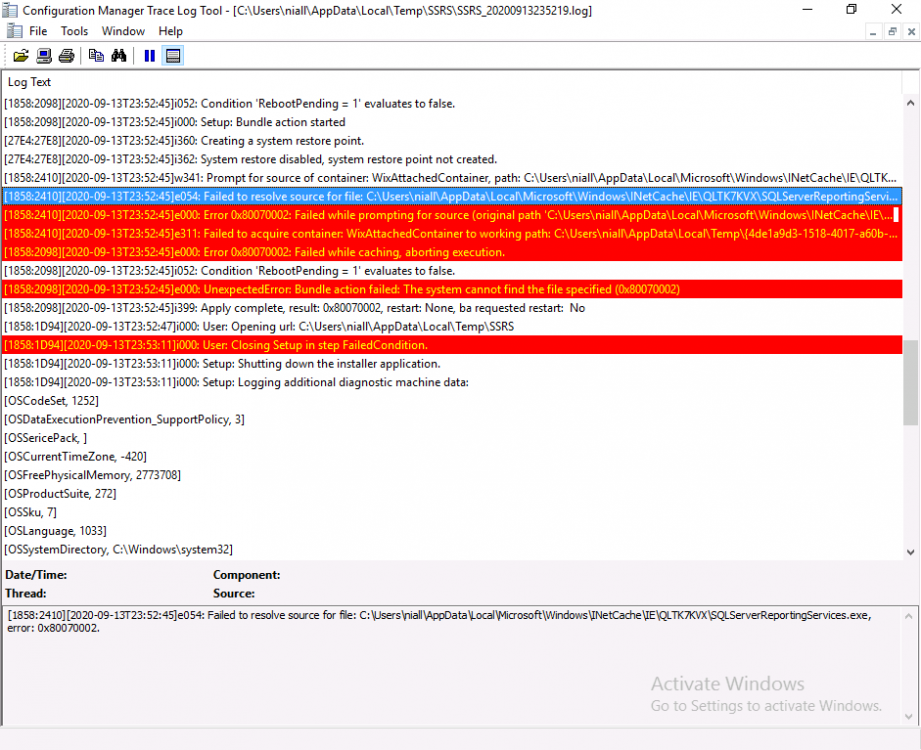
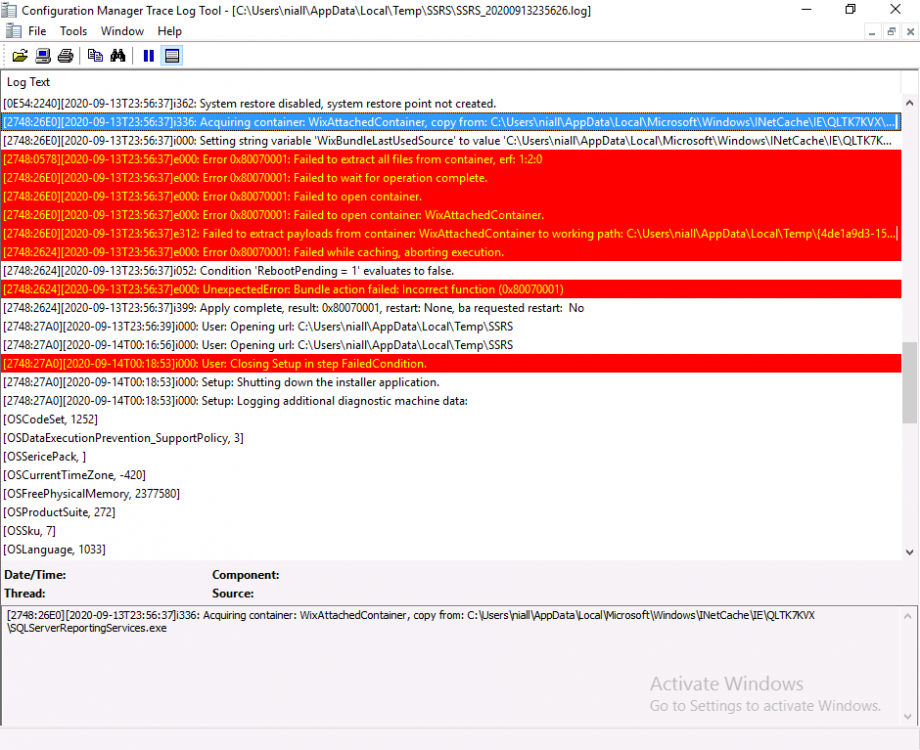
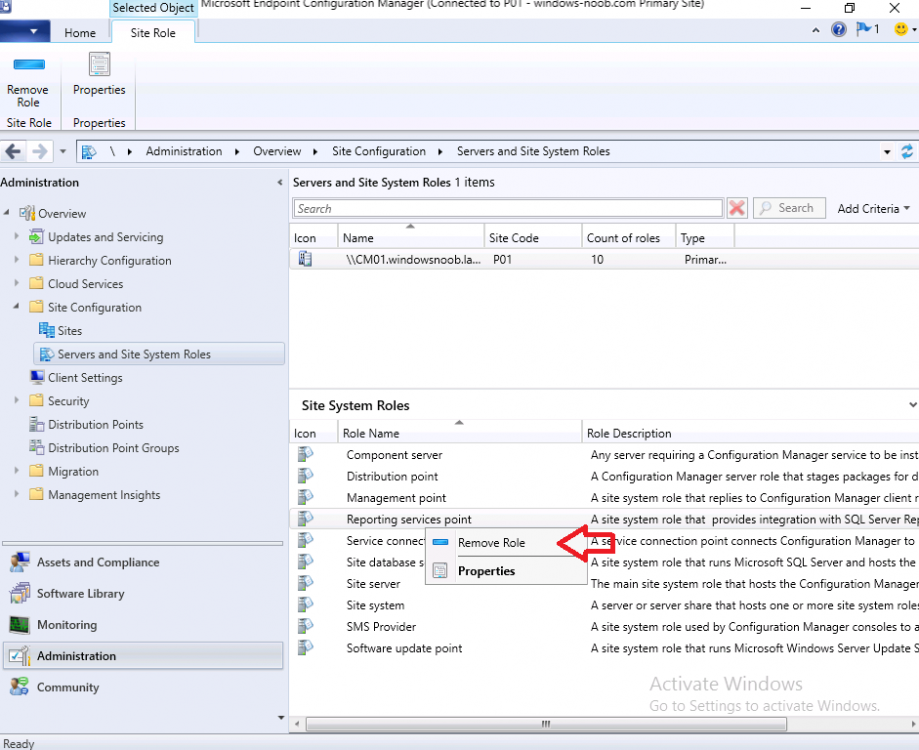
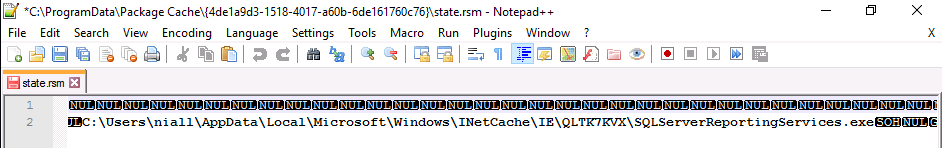
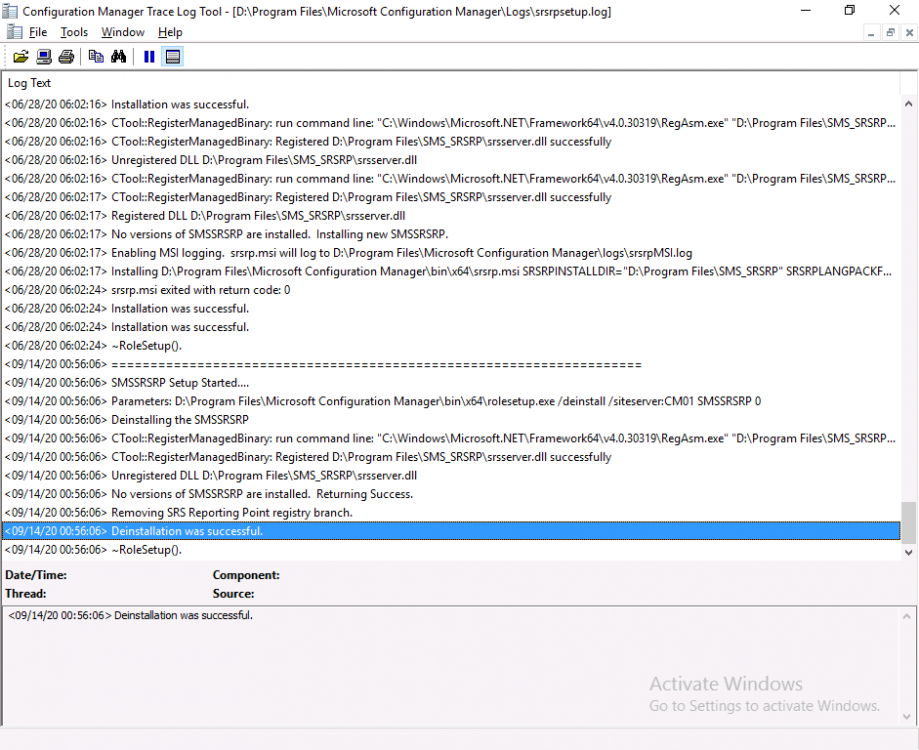
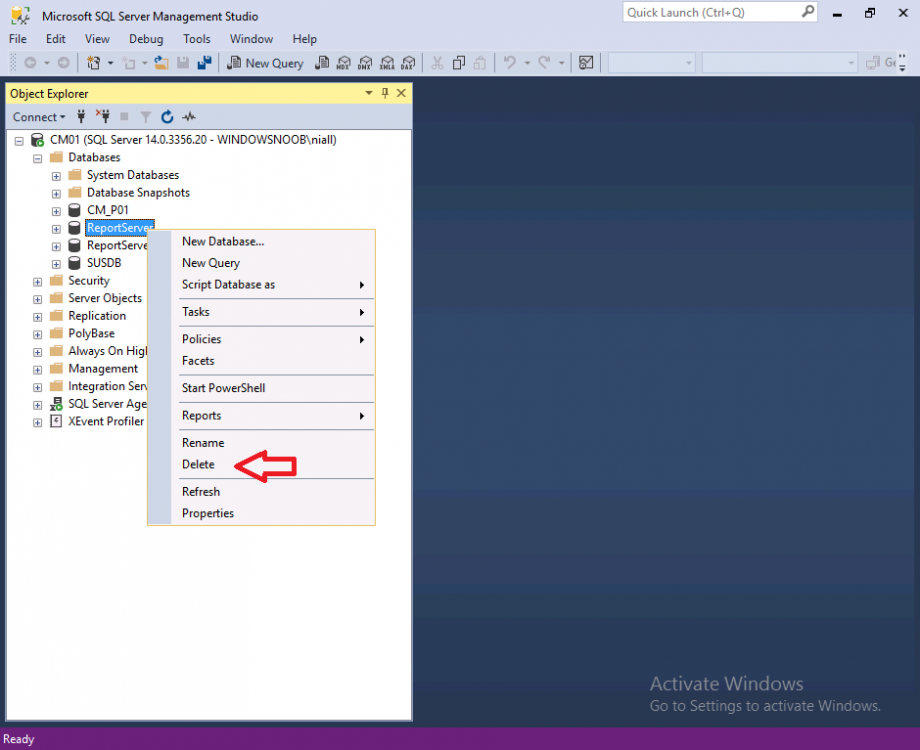
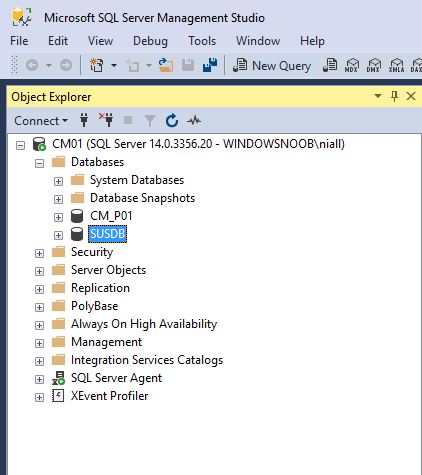
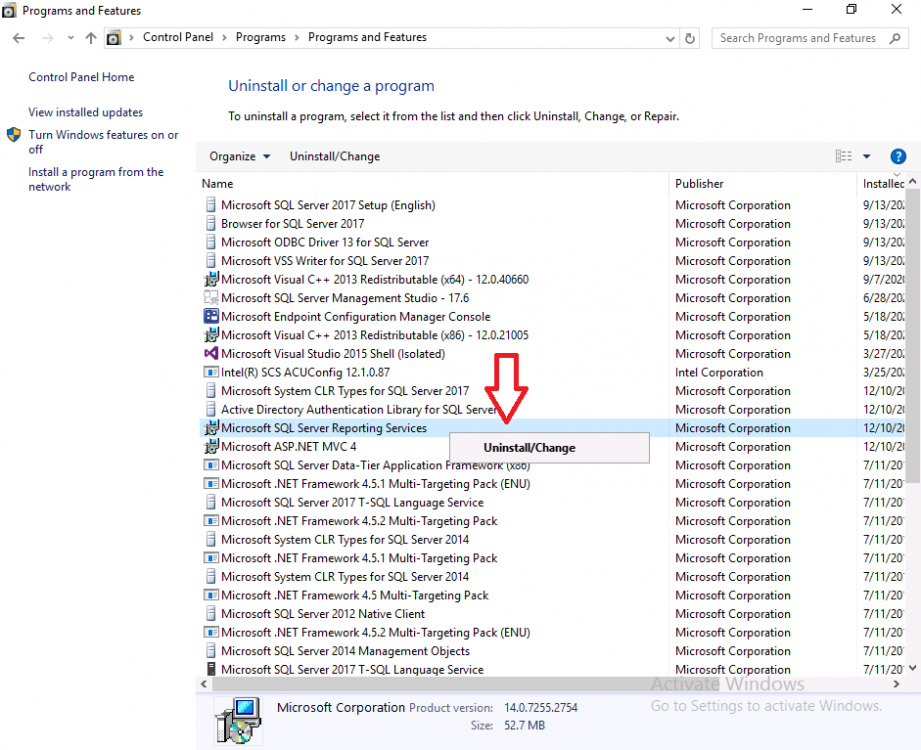
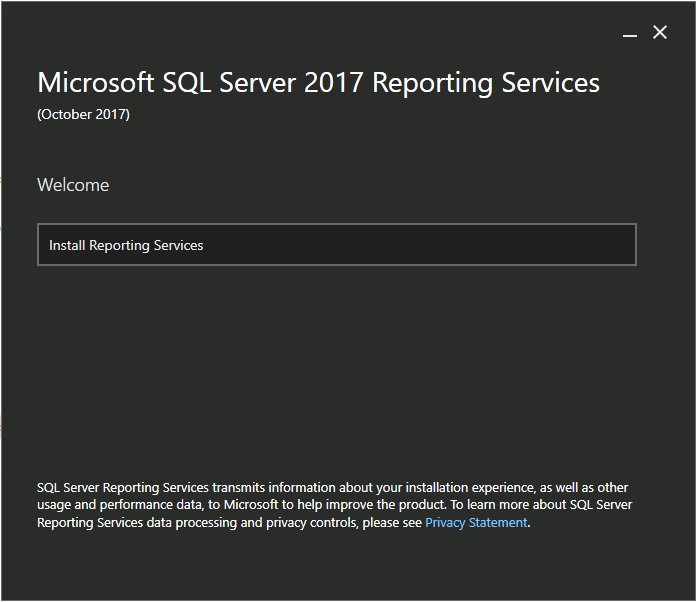
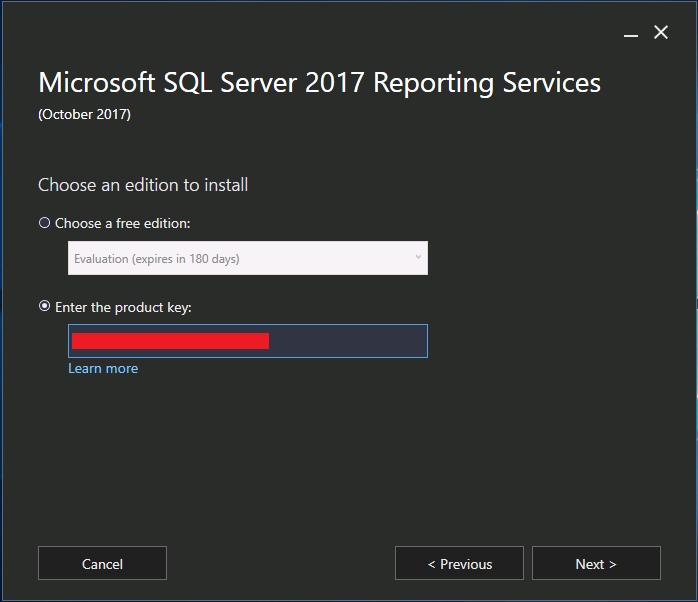
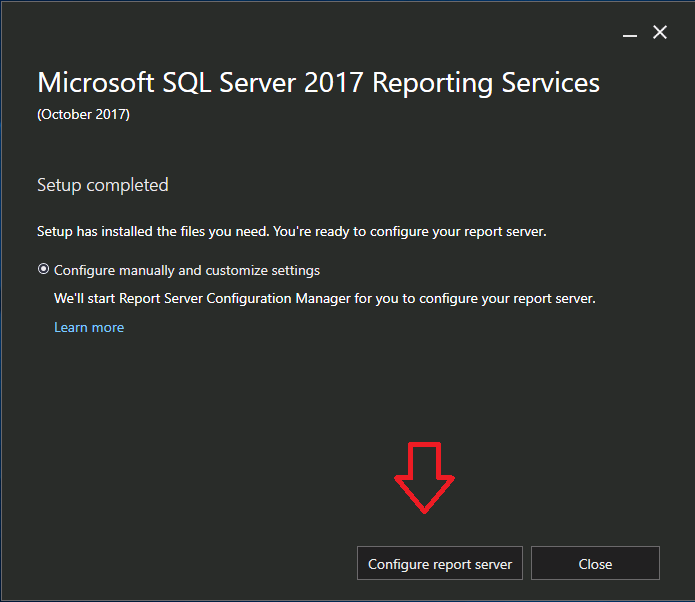
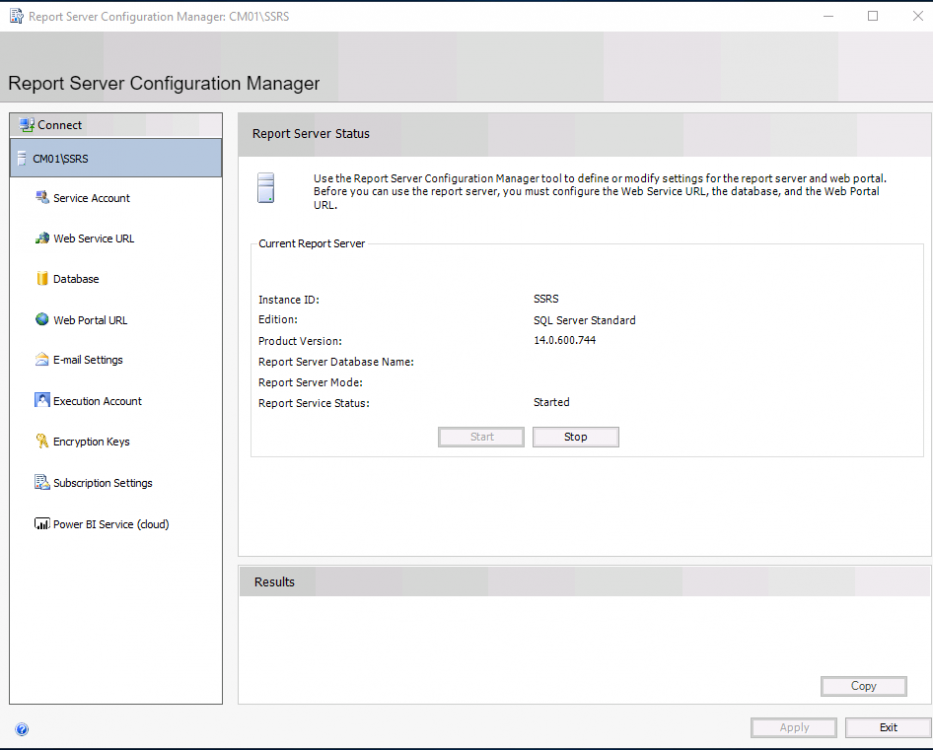
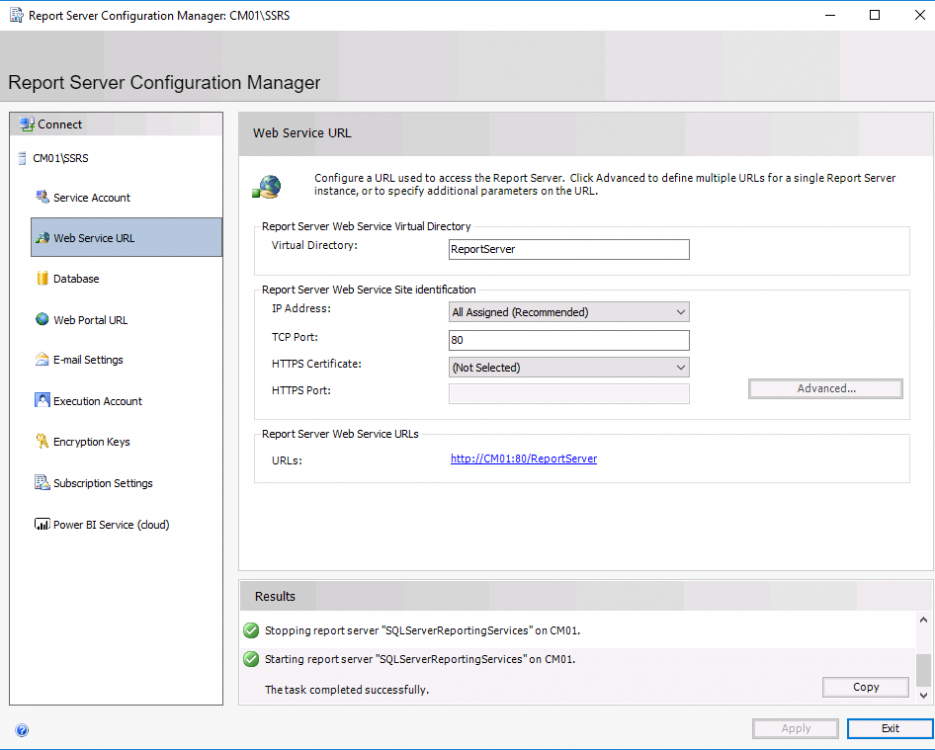
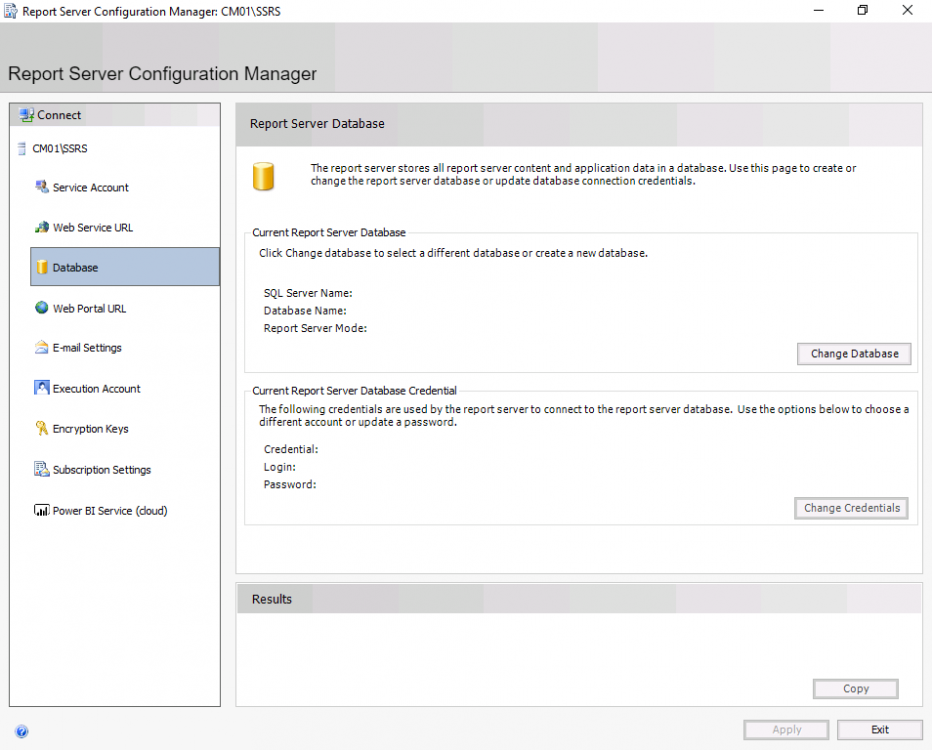
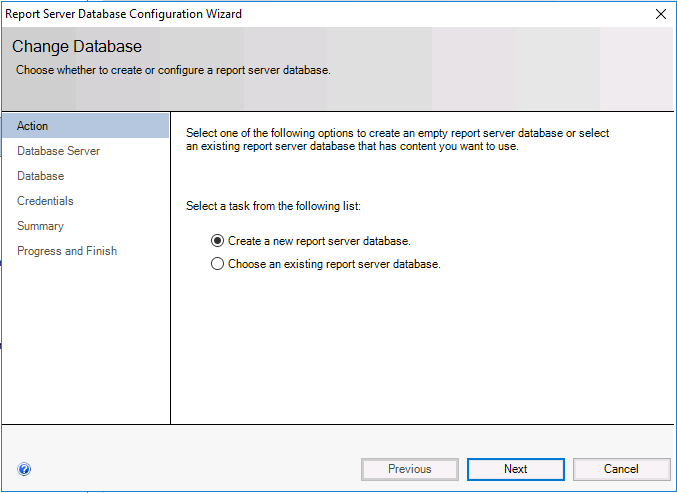
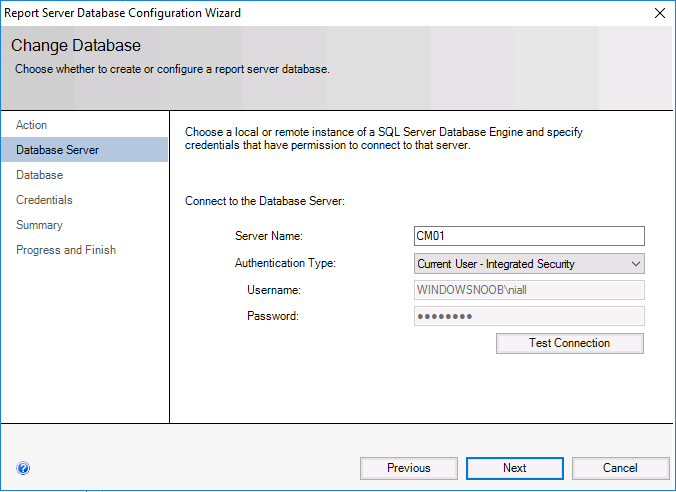
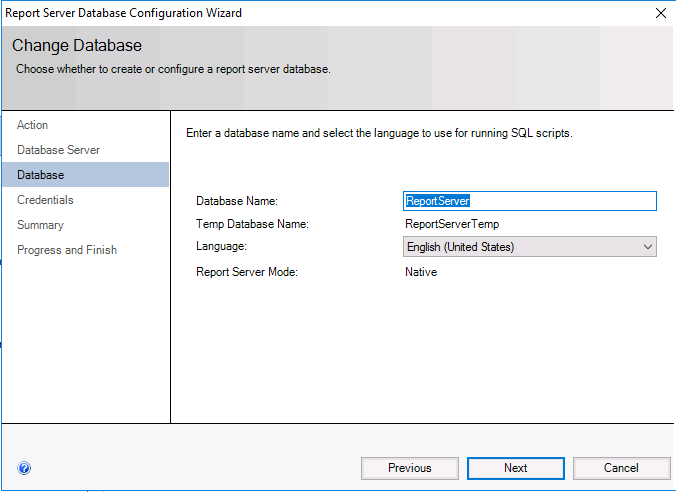
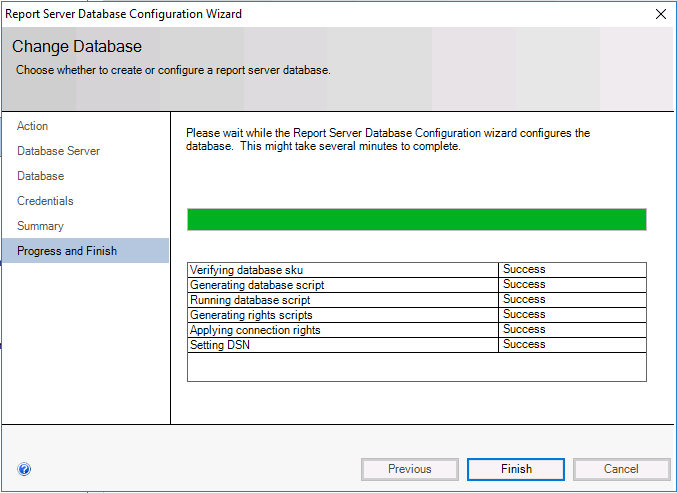
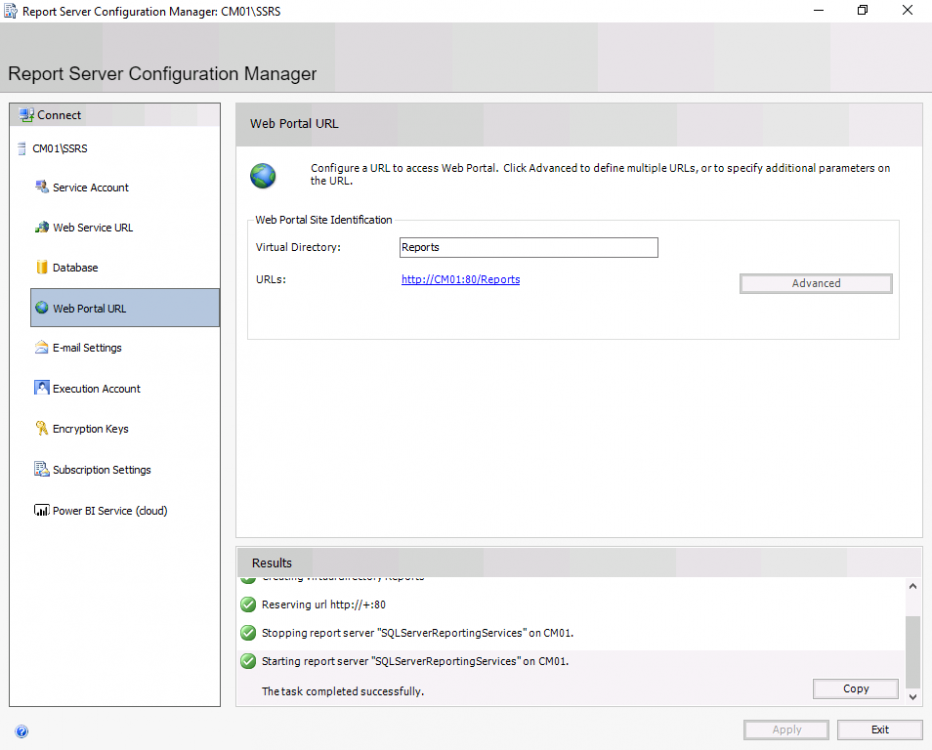
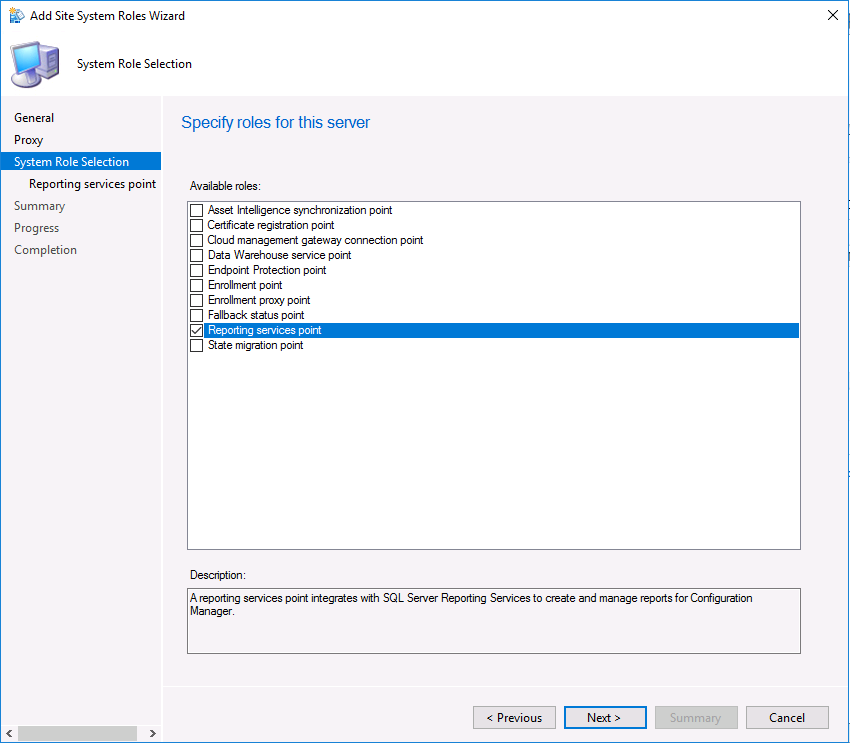
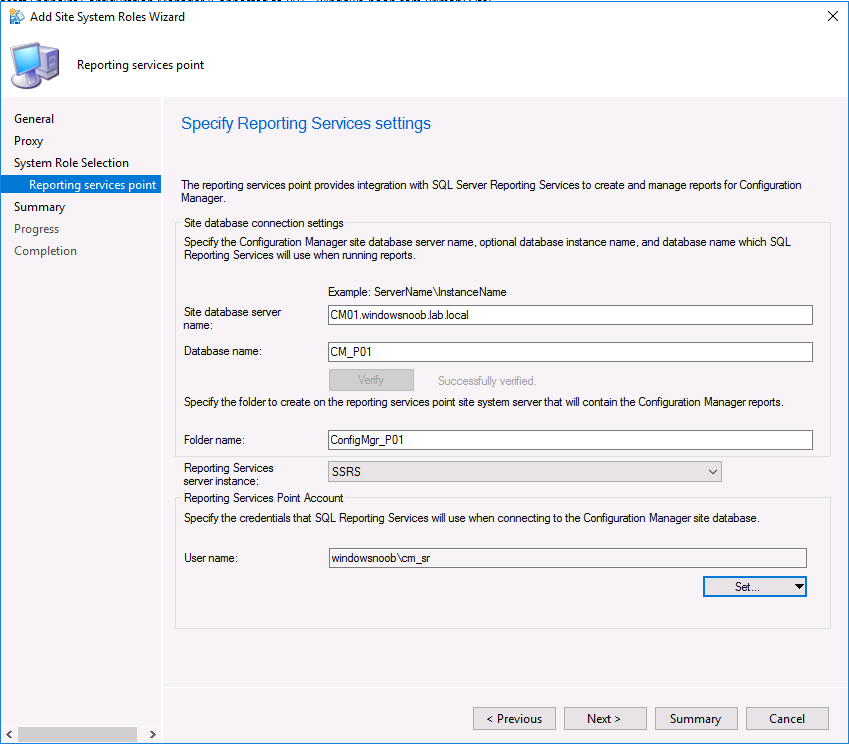
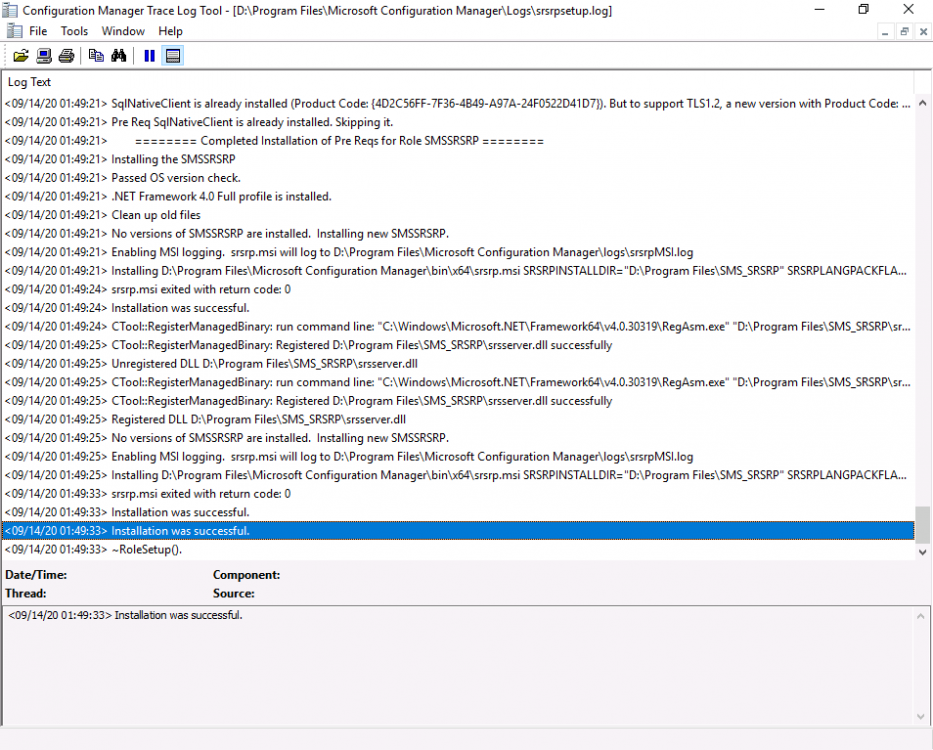
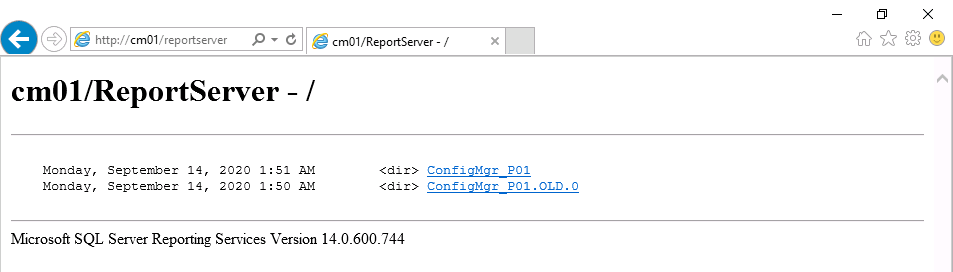
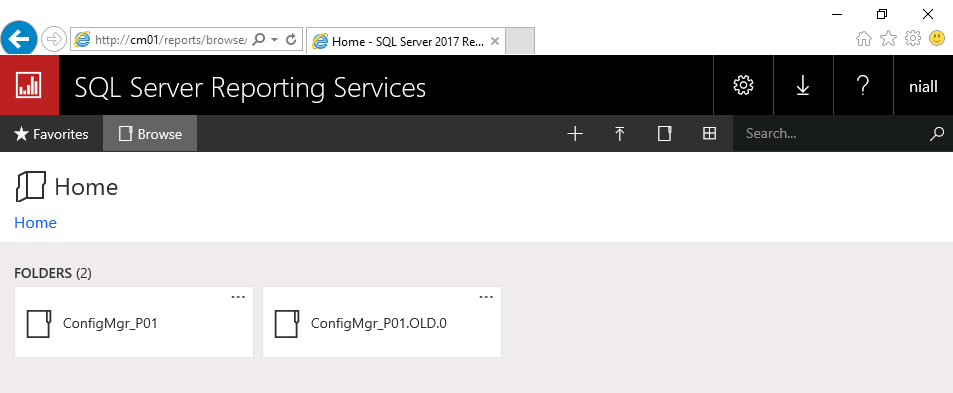
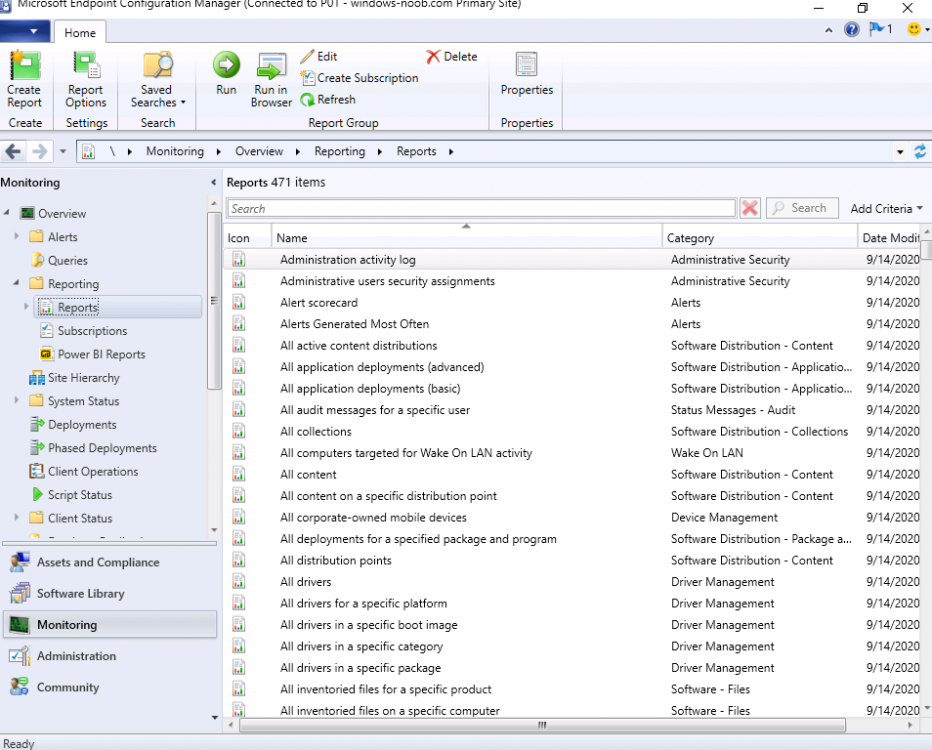
Introduction I was writing a blog post about Troubleshooting BitLocker Management in ConfigMgr 2002 Current Branch and one of the things I was trying to do was install the web portals, but I was seeing errors shown below. Get-ReportServiceUri : Caught exception querying report service at http://cm01.windowsnoob.lab.local/Reportserver I assumed this was because SSRS was not installed or configured but after checking the lab, I could see it was indeed installed and configured. However when I browsed the http://cm01.windowsnoob.lab.local/ReportServer URL in Internet Explorer it produced a HTTP Error 503. The Service is unavailable. A quick search gave some clues and things to try but in reality the reason it was not working was because: SSRS was installed in evaluation mode SSRS evaluation had expired This was revealed in the logs stored at C:\Program Files\Microsoft SQL Server Reporting Services\SSRS\Logfiles To upgrade the evaluation version you'd normally just need to upgrade the edition of SSRS from Evaluation to Production via change/uninstall in Control Panel, however the way this installation was packaged (WIX bundle) meant that it retained the original download link in a bundled file called state.rsm and that was looking in the IE cache as you can see in the SSRS installation log files That path no longer existed. Manually recreating that path and copying the SQLServerReportingServices.exe file to that path did not help, it reported another error. I could keep trying to hack my way around these errors or fix it once and for all. Fixing the evaluation version As this is just a lab I decided to rip SSRS out completely and then add it back. Note: If you are doing this in production then make sure to backup all your custom reports first and if necessary backup the reporting databases also. I decided to try the following: uninstall reporting from ConfigMgr delete the 2 reporting db's in SQL uninstall SQL Reporting Services in control panel restart server reinstall SSRS reconfigure SSRS Keep in mind that unless you want the same problem occurring in 180 days or so, you'll need the key that was used when installing SQL. If this process doesn't pick it up from your installed instance of SQL, you can find that key in the installation media. Using the product key from DefaultSetup.ini To find the product key in your installation media, you should know that the PID is more than likely contained within the DefaultSetup.ini file located under Root\X86 or Root\x64 folder. Open that file with notepad and copy the product key for later use. Let's get started. In ConfigMgr remove the SSRS role. Confirm that it's removed successfully via the SRSRPSetup.log. Next, in Sql Server Management studio, find the 2 reporting services databases and remove them, if you are doing this in Production, read my NOTE at the top of this section as deleting the two Reporting databases will result in the following: Reporting services will not work (it's broken already...), all your reports will have been lost (you did back them up didn't you ?), schedules, permissions, etc. And now they are gone. Next in Control Panel, locate SQL Server Reporting Services and uninstall it. Once uninstalled, close the wizard. restart the ConfigMgr server. After the server has restarted, reinstall SSRS by launching SQLServerReportingServices.exe available for download here for SQL Server 2017 or here for SQL Server 2019. After downloading it, copy it to a safe location outside of the browsers cache, eg: C:\SSRSSource. Run the executable and choose Install Reporting Services. Paste in your SQL License key from the SQL Server media, look in ..\x64\DefaultSetup.ini and your SQL license key will be in there. Accept the license terms Install the database engine. Pick the path and click next, after a while it's completed. Click on Configure Report Server. Select Connect when prompted. The report server configuration manager wizard will appear, notice how it states the version is Standard (and not evaluation). In Web Service URL, click Apply. Note: This is assuming you want to configure SSRS in HTTP mode, if you'd like to use HTTPS mode please review this blog post. For Database, choose Change Database. Choose create a new report server database from the options Decide if you are going to use the current logged on user or a SQL server account to setup this new database Select the database name. continue through that wizard until completion. Make sure it's all successful before clicking on Finish. Next, click on Web Portal, and choose Apply. And you can configure other options or simply select Exit. In the ConfigMgr console, add back the reporting services role Configure the account... And confirm that it was successfully installed in the SRSPSetup.log. At this point you can go back into your web browser and confirm that reporting is indeed responding without the initial error. Tada ! and via the Reports web portal. And finally, verify that the reports are present and working in the ConfigMgr console And that's it ! Once again I started one blog post only to hit an issue that threw me a wobbler. But thanks to that you have this blog post ?
-
The Backup Bible is an ambitious project produced by Altaro and written by Microsoft MVP Eric Siron that aims to be the definite guide to backup and disaster recovery for companies of all sizes. The first eBook in the series was published earlier this year and focused on how to create a robust backup strategy including the key stakeholders you’ll need to deal with and the questions you’ll need to ask yourself to prepare yourself for a potential data loss event. Part 2 – Backup Best Practices in Action – follows on from this starting point explaining how to implement this strategy and showing the reader what secure backup looks like on a day- to-day basis. The eBook is focused on providing practical implementation using actionable steps in each section providing the reader with the knowledge to bring the theory to life. It covers: Choosing the Right Backup and Recovery Software Setting and Achieving Backup Storage Targets Securing and Protecting Backup Data Defining Backup Schedules Monitoring, Testing, and Maintaining Systems And More! The Backup Bible is an essential resource for anyone who manages data on a daily basis. For any business, data is your lifeline. A significant data loss can cause irreparable damage. Every company must ask itself - is our data properly protected? You can download both part 1 and part 2 for free right now! The final part of the series, on disaster recovery, will be released later this year. By accessing the available parts, you’ll automatically receive the final eBook direct to your inbox when it is released later this year! What are you waiting for? Get your eBook now!
-
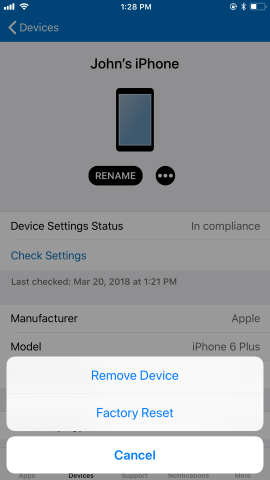
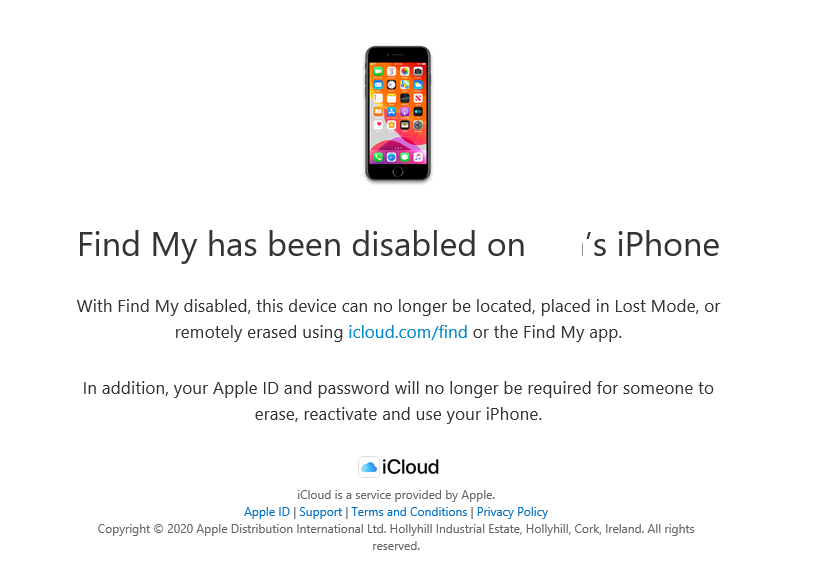
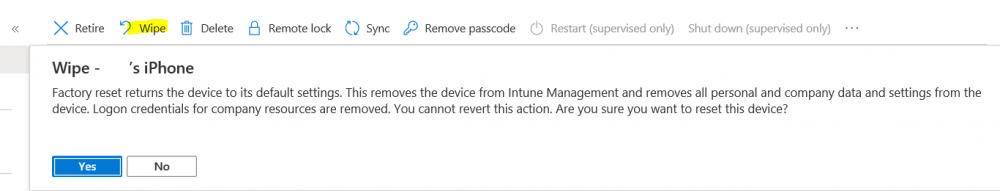
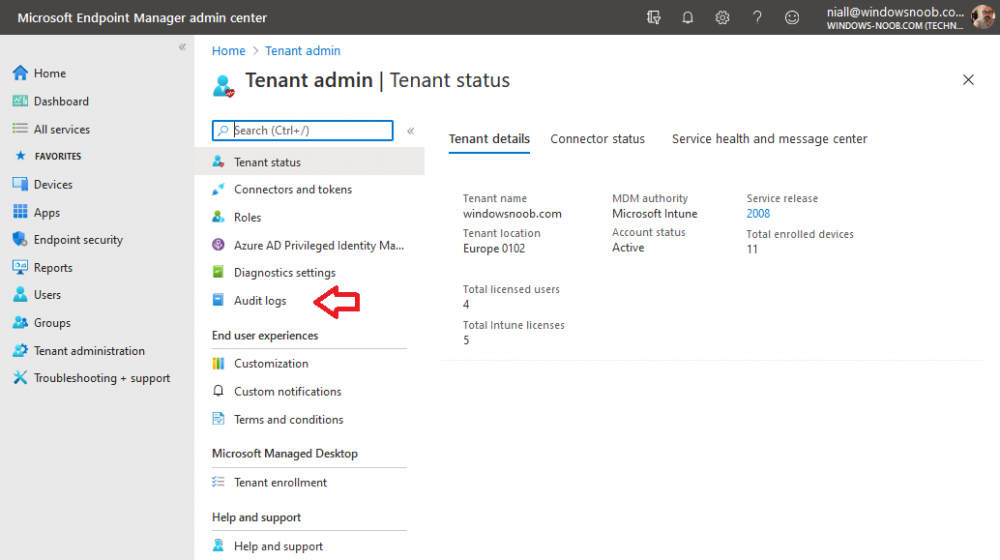
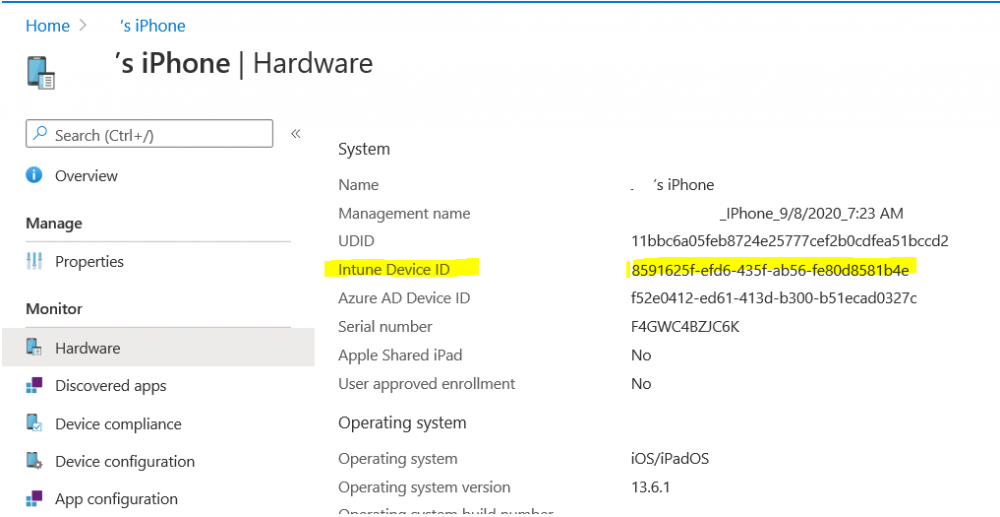
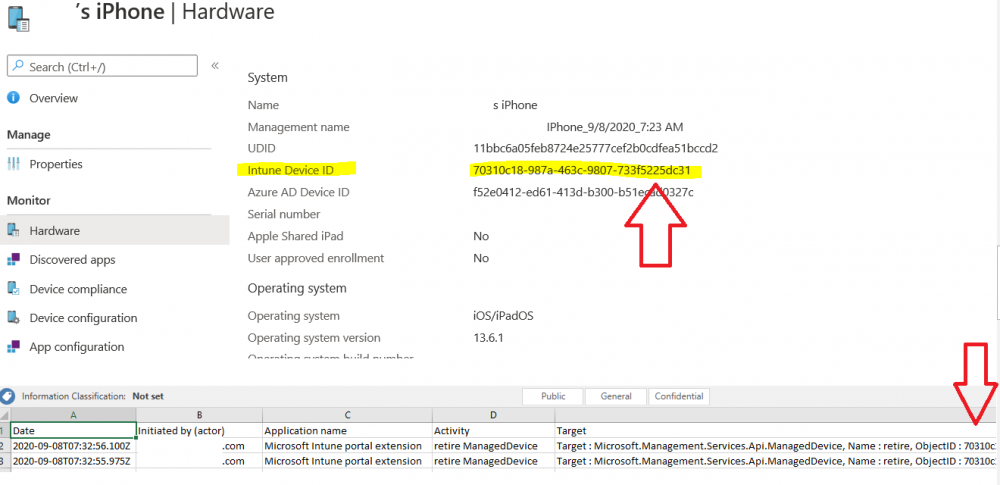
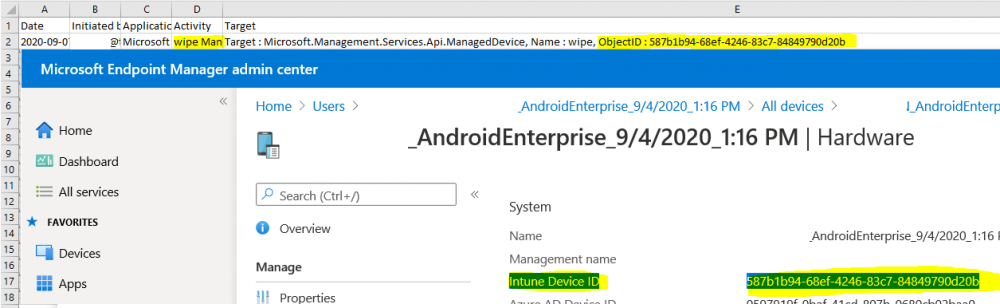
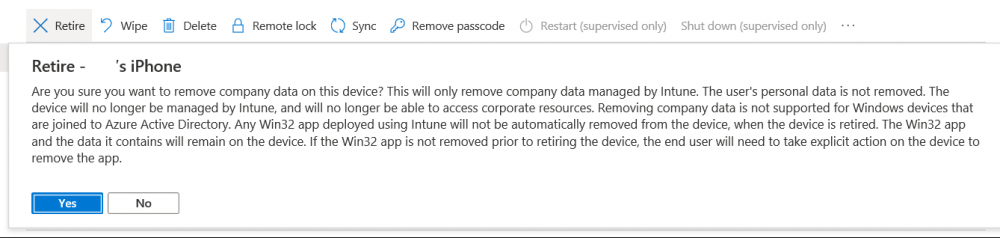
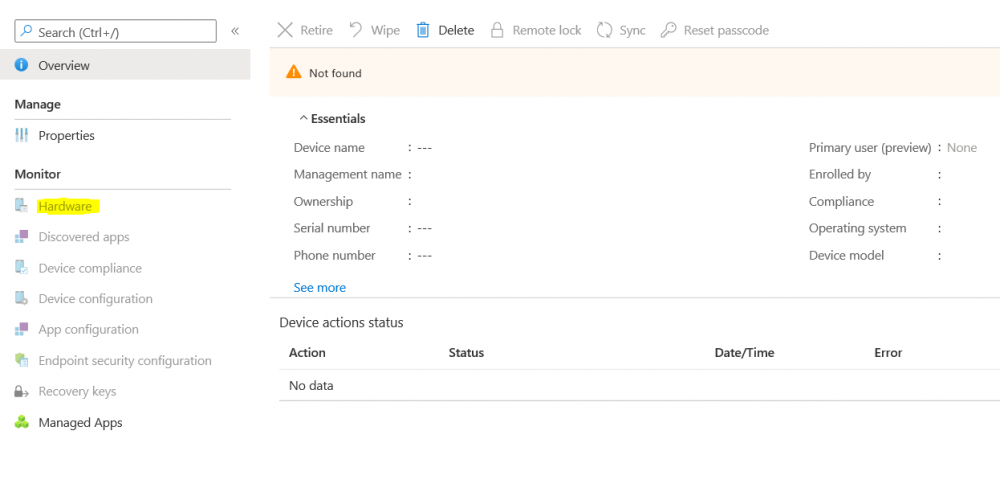
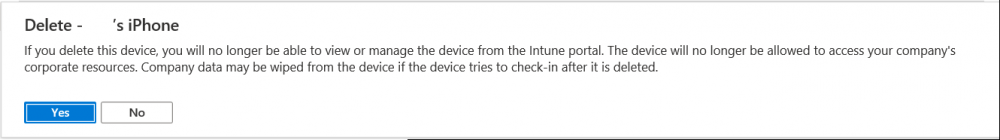
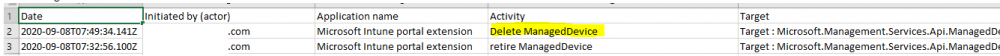
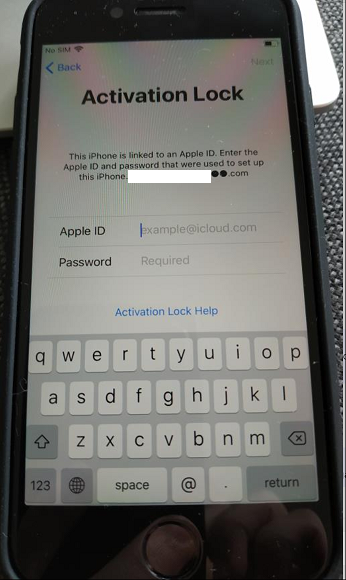
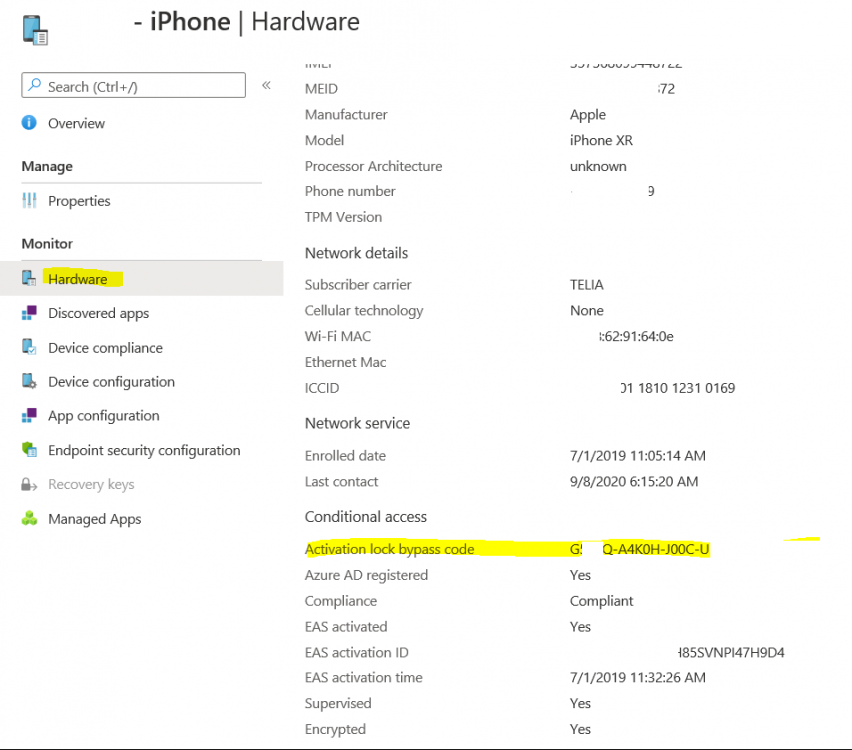
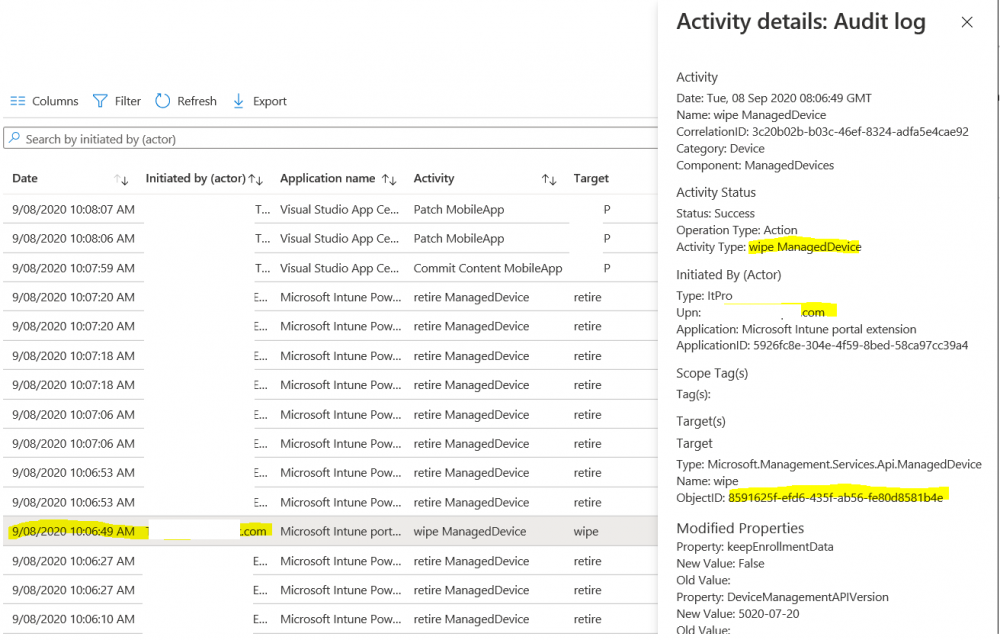
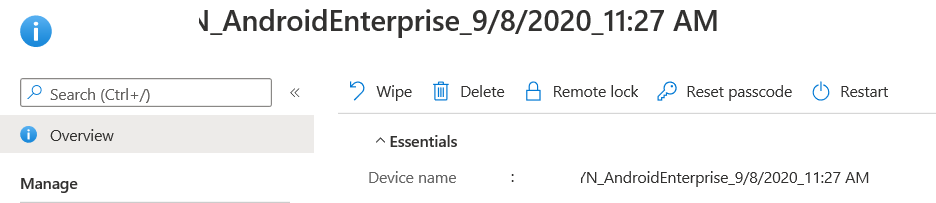
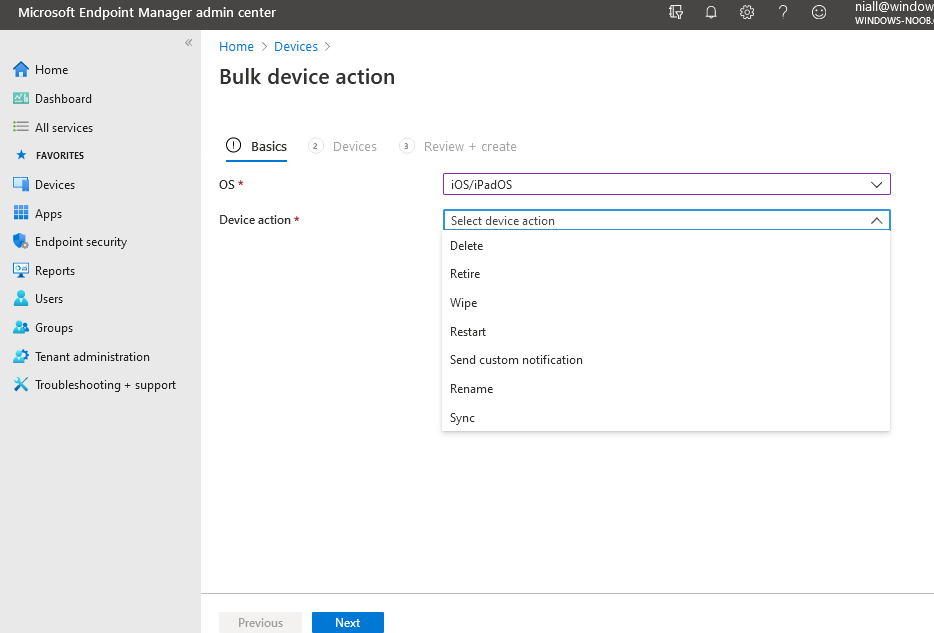
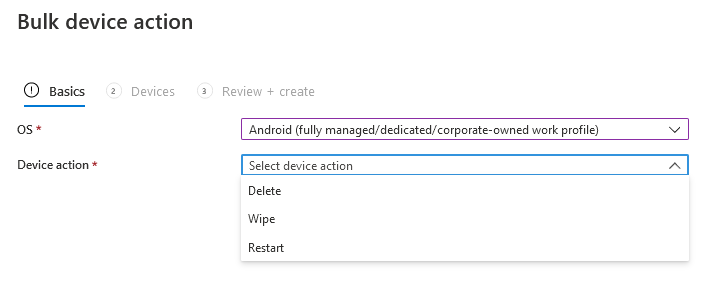
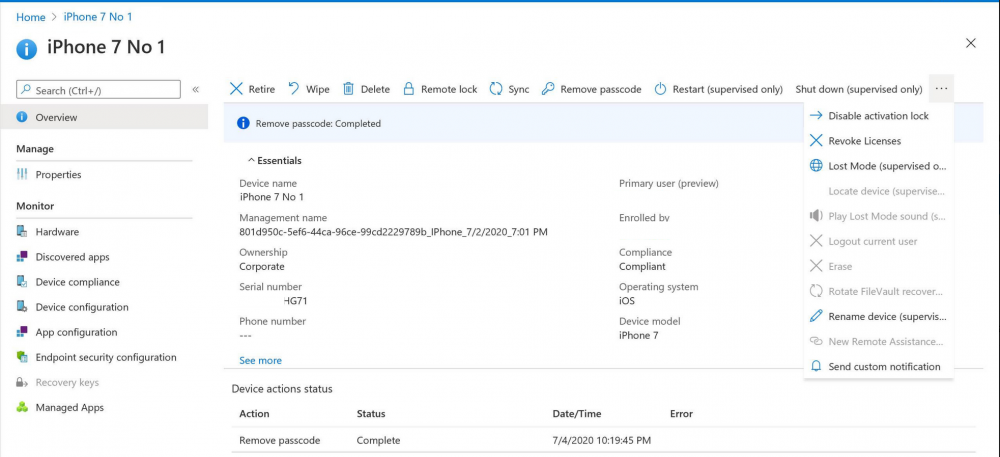
Introduction I wanted to better understand the options available for removing company data from phones enrolled within Endpoint Manager (formally known as Intune) so some research and testing was in order and that's exactly what me and my colleague did, additionally I wanted to get proof of the actions via the Auditing ability within Endpoint Manager. The phones involved in the testing were Company Owned iPhone and Android Fully Managed devices. There were a number of ways of removing company data shown below, and in this blog post I'll focus on the first two options, if you'd like to automate it with PowerShell then see my 2 links at the bottom of this blog post for information on how you can do that. User Actions on the phone itself Remote actions from within Endpoint Manager Remote actions using PowerShell via Graph User actions on the phone On the phone itself (iPhone) the user has a number of options available. They can open the Company Portal app, select the device from the list of devices and click on the 3 dots (elipse) to see actions available and those include Remove Device Factory Reset When you unenroll your device from Intune by selecting Remove Device, here's what happens: Your device won't appear in the Company Portal anymore. You can't install apps from the Company Portal anymore. Any settings that were changed on your device when you added it (for example, disabling the camera, or requiring a certain password length) will no longer apply. You might not have access to some company resources, such as file shares or internal web sites, on your device anymore. You can't use company apps and company data on your device anymore. You might not be able to connect to your company network using Wi-Fi or a virtual private network (VPN) anymore. Company email profiles are removed from the device. Devices that are configured for email only won't appear in the Company Portal app or website anymore. Apps are uninstalled. Company app data is removed. The process above is described here for iOS devices. https://docs.microsoft.com/en-us/mem/intune/user-help/unenroll-your-device-from-intune-ios Choosing the Factory Reset option prompts you to use the factory reset option within the iPhone settings app, and the result is that the phone is factory reset, company data is wiped, in fact everything is wiped including personal data, settings, etc, but the device is not immediately removed from Intune. Choosing this method should also prompt the end user for their icloud password to confirm that they were going to reset the phone, in addition they would receive an email from Apple indicating that 'find my' Iphone has been disabled. As regards Intune auditing of the events above, nothing was recorded as the phone was reset from the phone side and not via the Intune side (which reports on actions related to wipe, delete, retire performed via the console or via a PowerShell script). Removing the device management profile In addition, we tried removing device management, via Settings, General, Device Management and removed the MDM device management profile, this did not reset the phone but removed access to company resources and removed all apps associated with the company. The users personal data remained unchanged. The device (shortly after) showed as non-compliant in Intune/Endpoint Manager and could be automatically removed via the device cleanup ability. Using this method again did not record anything in Auditing. Note: Device cleanup rules aren't available for Android Enterprise scenarios like Fully Managed, Dedicated, and Corporate-Owned with Work Profile. Using actions from within the Endpoint Manager console In Microsoft Endpoint Manager, you have additional options to remove company data from enrolled phones, and these are as follows: Wipe Retire Delete Let's look at each action to see how it relates to the device in question. Wipe This option completely factory resets the phone, does NOT prompt for the users icloud password and all user data and company data is removed. The phone reboots as part of the process. Below is a typical display of what you'd see when you initiate the Wipe action from within Endpoint Manager. As this action took place from within Endpoint Manager, it will be recorded in the Audit Logs. You can find these logs in Tenant Administration, Audit Logs as shown below. After a Wipe is performed in Endpoint Manager, the action (and more details) are recorded in the Audit logs as shown here. You can click an individual action to get a details pane. In the screenshot above, the Activity details refers to an ObjectID and that is actually the Intune Device ID as shown here. So if you want to trace a phones removal from Endpoint Manager, then make sure you've a backup of this information so you can co-relate the Intune Device ID with the ObjectID listed in the audit log. Here you can see the same info relating to the Intune Device ID in the console and the Object ID in the exported CSV file for an Android phone when it's Wiped. You can export the audit log (up to a months data in the console or 1 year via PowerShell Graph) to a CSV file. Remember, take note of the Intune Device ID before you Wipe a phone as once it's wiped the data will also be removed from Intune. In the screenshot below you can see the details remaining for a phone that was just wiped, notice how it states 'not found' and the Hardware node is greyed out, in the hardware node you'd normally find the Intune Device ID but now that the device is wiped, the data is gone. Retire The Retire option removes company data, keeps personal data and does not reboot the device. Below is the prompt received when you select to Retire an iPhone. And below you can see how the Retire option is audited (via the exported CSV file), and again i'm pointing out the Intune Device ID in the console as it's the Object ID in the audit log. Interesting to note that the Intune Device ID (object ID in the audit log) changes every time you enroll the device. In the console itself the device is removed as soon as the next device check in occurs. Note: If you are using Fully Managed for your Android devices then you won't see a Retire option at all. Delete Selecting Delete will prompt the admin with something similar to below for iPhone. and the delete action is audited also. However when I did the Delete action for an Android Fully Managed device, it reset the phone (factory reset) which goes against the popup prior to the action. Bulk Device Actions There is one other way of doing this but it's more risky as it applies to all devices, and that is the ability to choose the available actions (thanks @JeffGilb ) which is available in Bulk Device Actions You can then select the type of device and the action available, here are the options available for iOS/iPadOS and below are the actions for Android (Fully Managed) Summary Deciding which path to take should be based on your security needs and the ultimate destination of the phones after they go EOL. If your company phones are all iPhone based, you may want to choose either Retire or Delete from the Endpoint Manager console (or using a PowerShell script to connect to Intune using the Graph API), as these actions will be logged in the Audit logs (which can be exported for up to one year), and both of these actions are least disruptive to the users phone, as the users data (photos/apps/etc) will remain on the phone but all company data will be removed. This would be suitable in a scenario such as where personnel are giving the option to buy back the company device after it's EOL. Take note however that the Delete option on Android Fully Managed phones also factory resets the device (all data personal and company is removed). That is not expected based on the popup shown to the admin. If for security reasons you want to remove all company data and all personal data AND remove corporate logon details then you should choose the Wipe option as this does a factory reset on both iphone and Android (fully managed) phones, and this will be audited in the audit logs. This method however will not prompt iphone end users to sign out of icloud meaning that after the reset, the phone will be locked to the apple ID of the previous user (as shown below). To resolve this problem you could ask the user to sign out of icloud prior to Wiping the phone (not ideal) or use Apple Business Manager (DEP) to manage the phone, that way you'll get an Activation Bypass lock code which you can use to bypass this activation lock. Below is how that code would appear for a device (obfuscated details) in Intune. Of course this also means that you'll need a script to pull the Activation lock bypass code from Intune regularly (scheduled task) so that you have the data before it gets removed from Intune. Speaking of ABM enabled iPhones, once they are added into ABM you'll see additional options displayed in Intune such as those shown here, the additional options include (and more depending on the device and capabilities): Disable activation lock Lost mode (supervisor only) Rename device (supervisor only) Restart (supervisor only) Finally, if you get your users to remove the device management or factory reset their phones using options available on the phone itself, then there will be no record of that action in Intune so you won't be able to report on it. I hope this helps you understand the options available today in Endpoint Manager for removing company data on enrolled phones. Recommended Reading https://docs.microsoft.com/en-us/mem/intune/user-help/unenroll-your-device-from-intune-ios https://docs.microsoft.com/en-us/mem/intune/remote-actions/devices-wipe https://support.apple.com/en-us/HT202804 https://www.niallbrady.com/2017/08/23/getting-started-with-microsoft-graph-and-using-powershell-to-automate-things-in-intune/ https://www.niallbrady.com/2018/10/10/learn-how-to-leverage-intune-support-for-microsoft-graph-and-powershell-to-enable-powerful-automation-and-it-security-my-notes/ cheers niall
-
hi @ChrisFromBavaria I have not tested this on Windows Server 2019 Core edition, only on the Desktop Experience edition. you can only use the Distribution Point role on Server 2019 Core Edition, so this probably explains why it's just not working. Server core installations The server core installation of the following server OS versions are supported for use as a distribution point: Windows Server 2019 (starting in Configuration Manager, version 1810) Windows Server, version 1809 (starting in Configuration Manager, version 1810) Windows Server, version 1803 (starting in Configuration Manager, version 1802) Windows Server, version 1709 (starting in Configuration Manager, version 1710) Windows Server 2016 Windows Server 2012 R2 Windows Server 2012 This support has the following limitation: Distribution points on this OS don't support PXE or multicast with the default Windows Deployment Services. Starting in version 1806, you can PXE-enable a distribution point on this OS with the option to Enable a PXE responder without Windows Deployment Service. For more information, see Install and configure distribution points.
-
returning to this, @tasmo I found the cause, you need to add cmd.exe /c in front of the reg add command when using the %date% or %time% variables in the task sequence
- 242 replies
-
- 1702
- forced upgrade
-
(and 2 more)
Tagged with:
-
do you have teamviewer so i can remote in and take a look ? is 192.168.11.100 the local ip address of your webserver ?
-
whether it responds to ping or not doesn't really matter, what does matter is whether you can reach your pki.mydomain.com though, and clearly if it's not working for you, then your port forwarding via Vyos must be configured incorrectly, double check the settings and verify that it's forwarding port 80 to the local ip address of your webserver hosting the crl you can test this by using https://canyouseeme.org/ to verify if your port 80 is indeed open when testing browsing to the webserver url, you must disable WIFI on your phone and use your 3g connection
-
what is not working exactly ? be specific, I've gone through this lab multiple times and it works every single time.