-
Posts
9258 -
Joined
-
Last visited
-
Days Won
371
Everything posted by anyweb
-
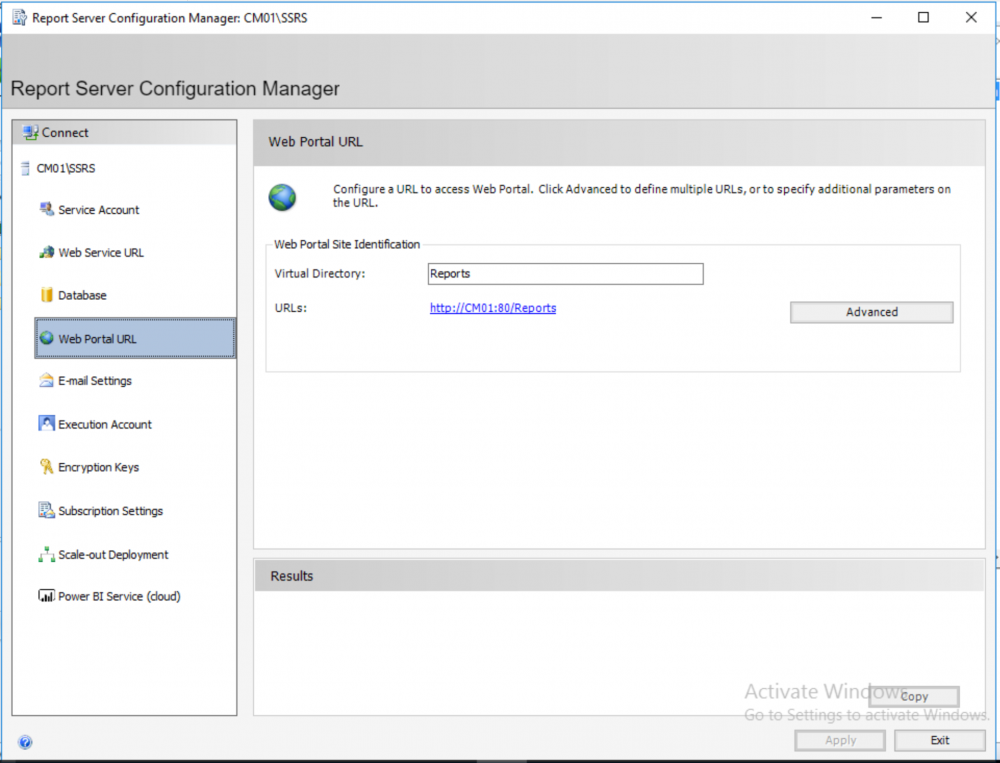
ok that's odd, so are you getting errors on all the 5 bitlocker reports ? do all other non-bitlocker reports render correctly for the same user ? lastly, have you looked at this post to see does it give you any pointers https://www.niallbrady.com/2019/11/12/a-quick-look-at-reporting-in-mbam-integrated-with-microsoft-endpoint-manager-configuration-manager/
-
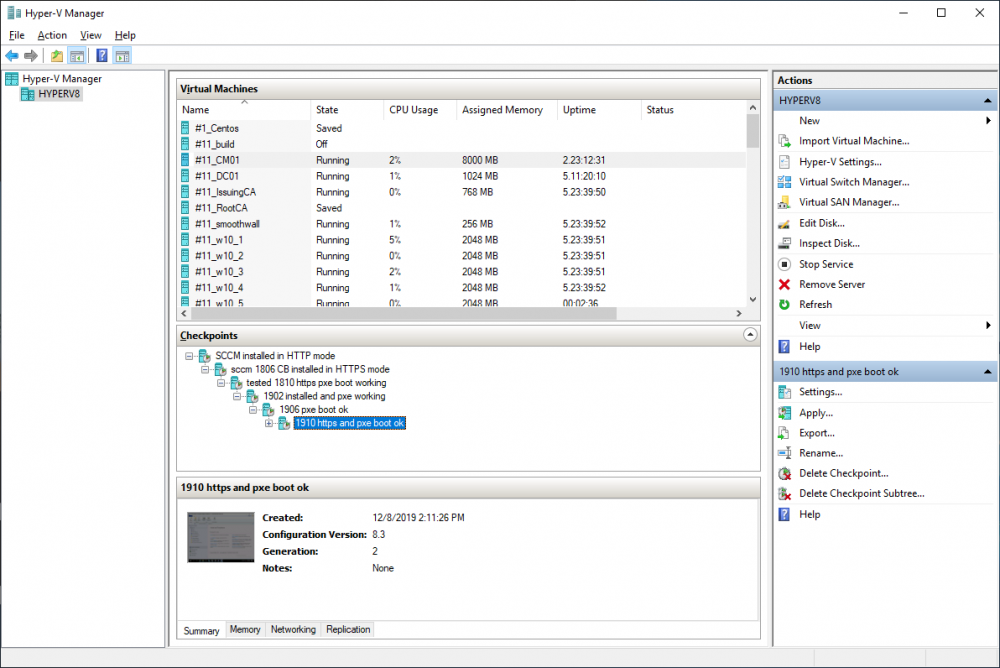
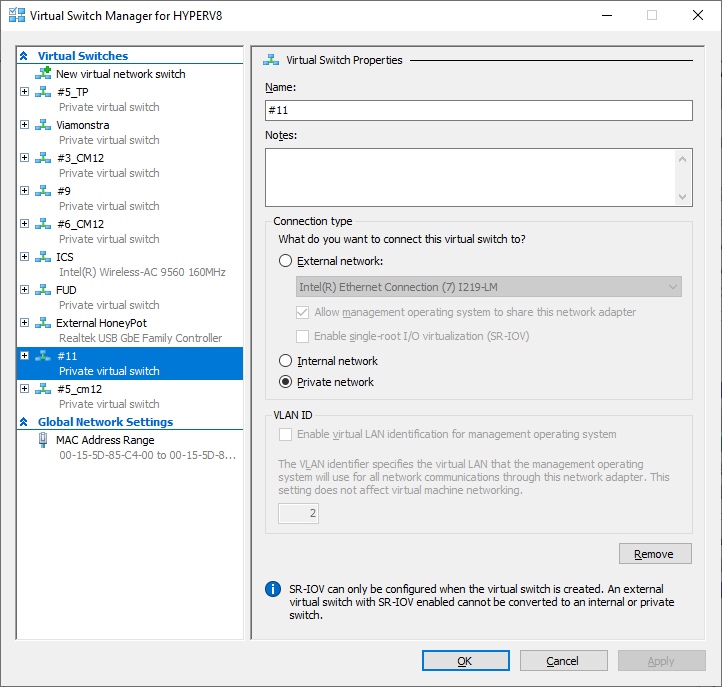
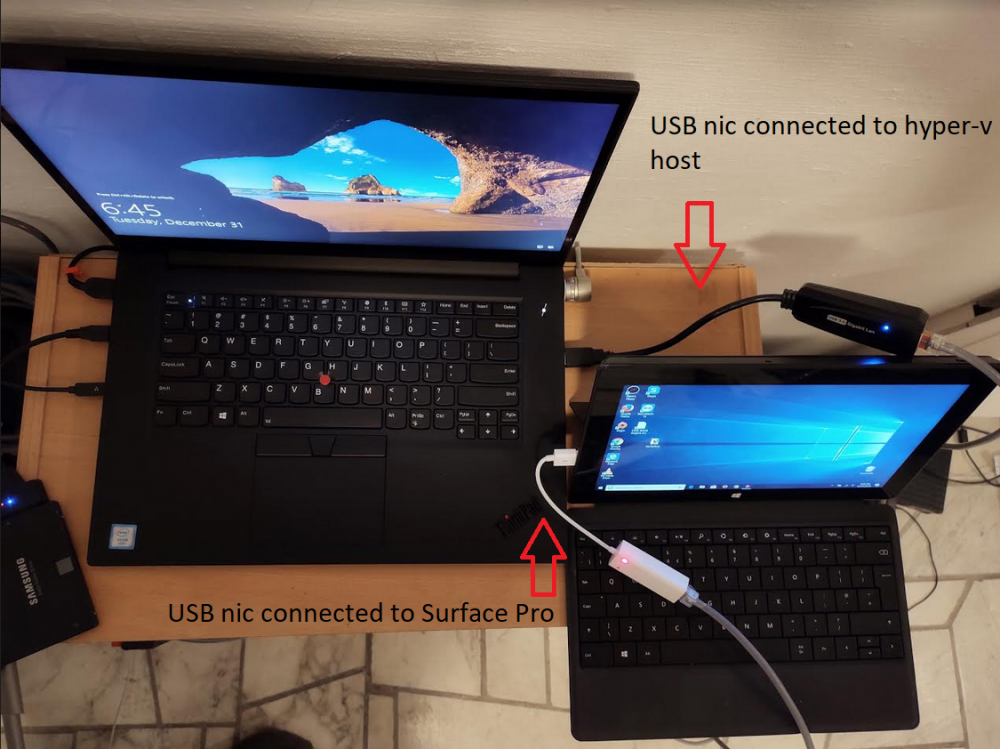
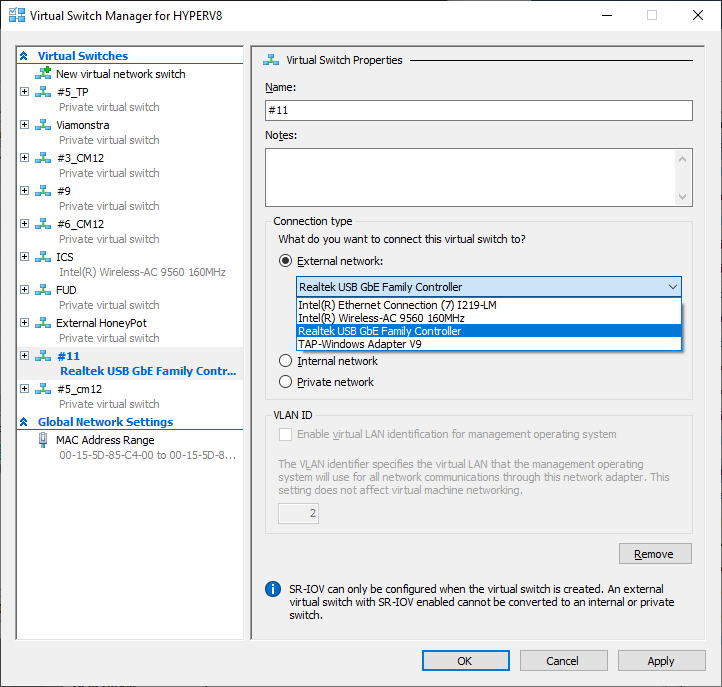
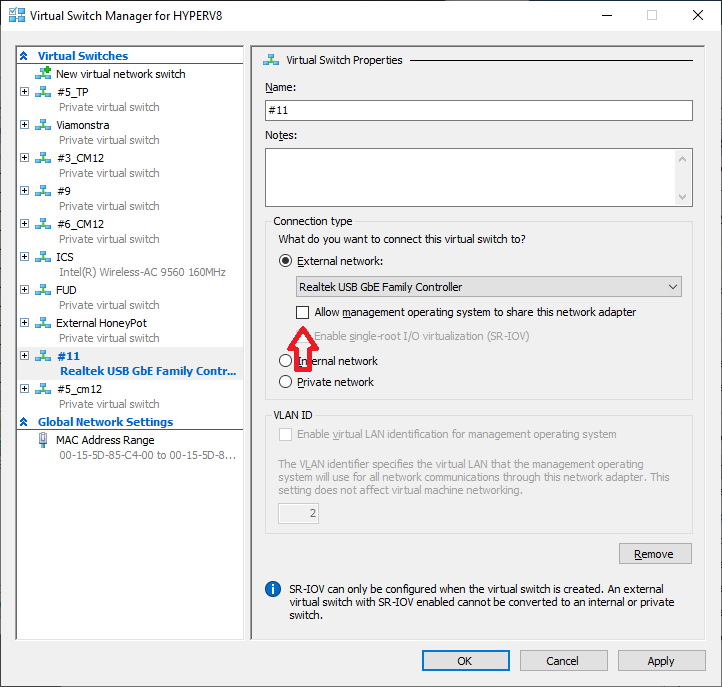
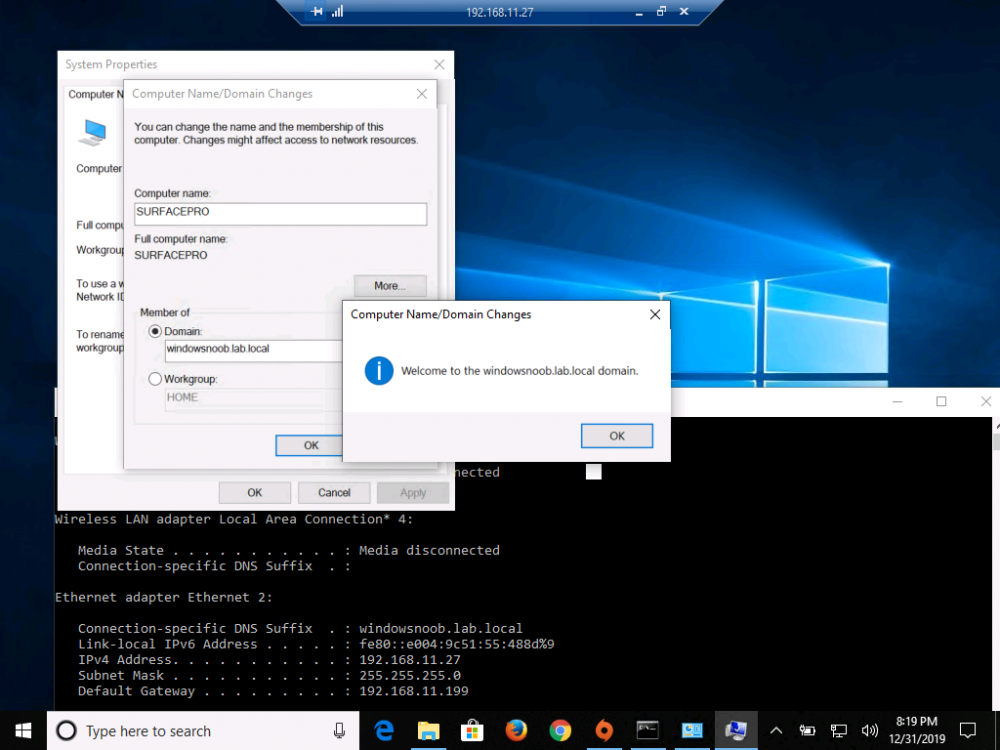
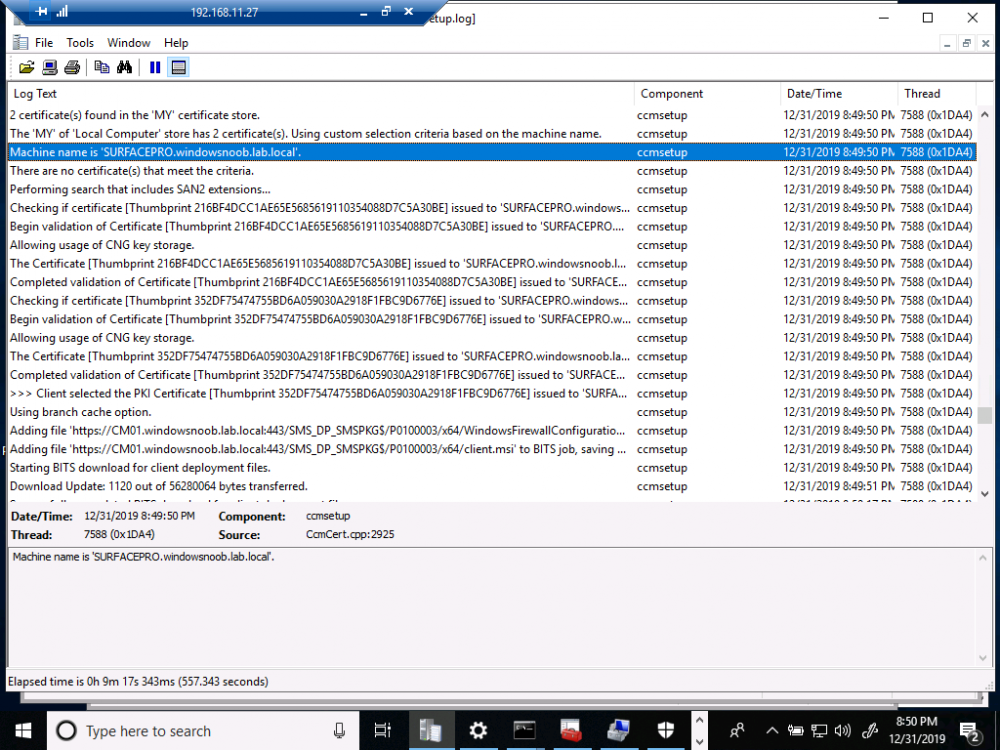
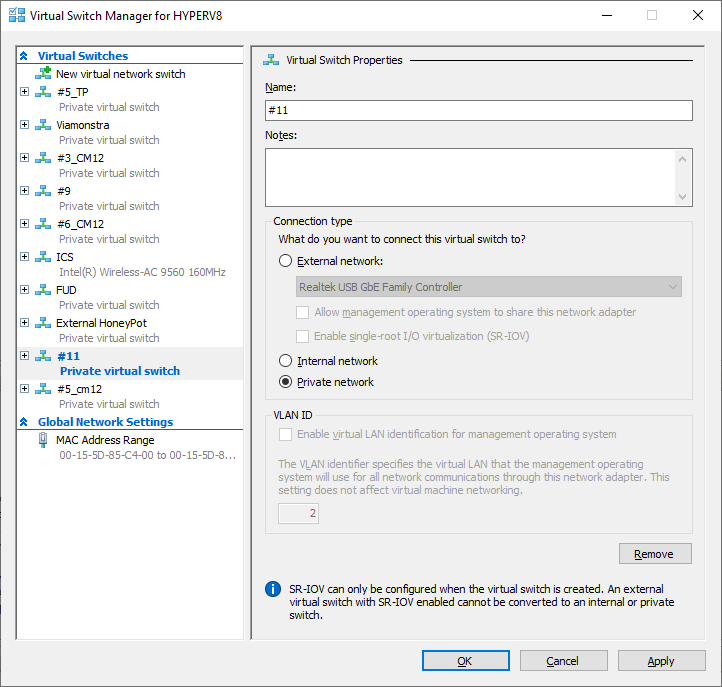
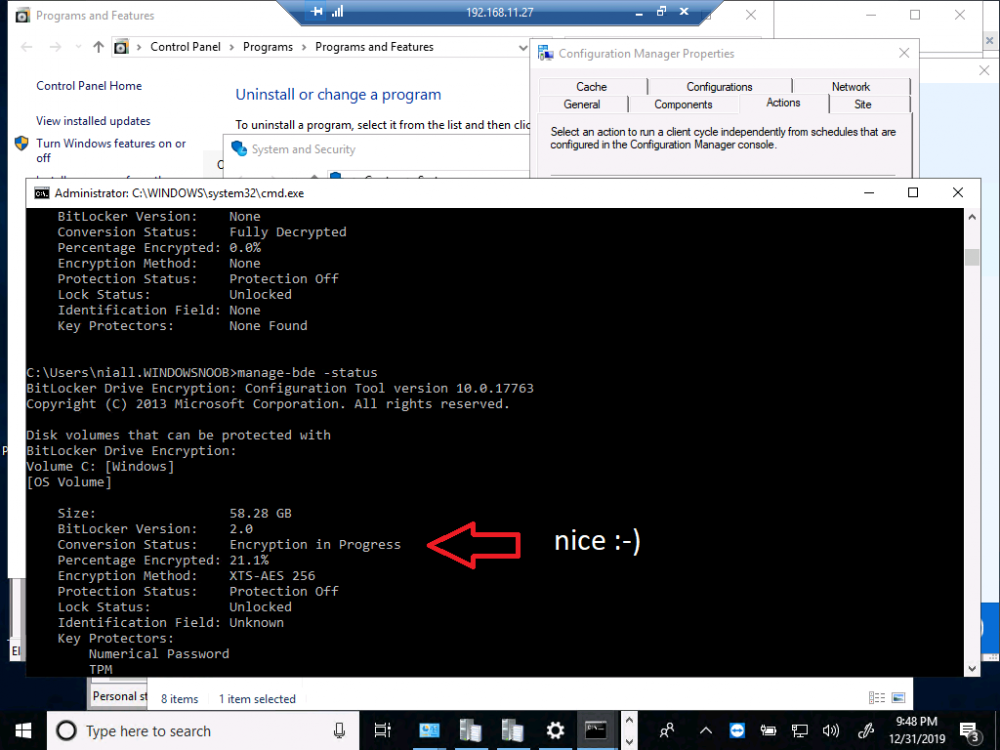
Introduction I occasionally want to connect real physical computers directly within one of my hyper-v based virtual labs to test various functionality within that lab which may require real hardware. A good example of that is testing MBAM Bitlocker management via Microsoft Endpoint Configuration Manager version 1910. This post will show you one way of connecting physical hardware to your internal hyper-v lab easily. Note: There are other ways of doing this, but this is really easy and quick and I thought i'd share it with you. Requirements To get the job done, you'll need some equipment, here's a small list. A hyperv host A working lab A physical computer to connect to your lab 2 USB network cards 1 network cable Optional: a DHCP scope inside your lab to share IP addresses to the real physical computer Optional: a Switch or hub if you want to connect more than one physical device Step 1. Connect the physical computer to the hyper-v host Here, I simply connect the network cable above to the 2 USB network cards, and plug one USB nic into the physical computers' USB port, and the other USB Nic into a free USB port on the Hyper-v host. the hyper-v host in this photo is the amazing Lenovo P1 laptop on the left of the picture, the 'physical computer' is the old Surface Pro computer. Step 2. Identify your labs virtual switch In Hyper-v, locate the lab you want to use. In the screenshot below, I'm going to use lab #11 for this as it's my main Microsoft Endpoint Configuration Manager (Current Branch) lab for testing MBAM functionality. In the right pane of the Hyper-v management console, click on Virtual Switch Manager to see your configured switches. Here you can see the virtual switch which I'm using for the #11 lab, it's called #11 and it's a private network. Note: If the USB nic used for this external access is already in use on your hyper-v host on another network switch, such as mine is, on the External Honeypot, you should first remove it from that network switch before trying to assign it to another network switch. Step 3. Change the network connection type Now that you've identified the target network switch, you can now switch the network connection type temporarily for the period of your test. I like to keep my labs on a private network unless otherwise called for, such as for this test. Set the connection type to External Network and next, select the USB nic from the list of available network cards, that is physically connected to your hyper-v host. Once done, de-select the option to Allow management operating system to share this network adapter. Click Apply when done. Step 4. Utilize the lab network on a physical computer Now that you've connected a physical computer to the internal hyper-v host lab, you can do whatever testing you hoped to carry out. In the below screenshot I have used RDP to connect to the physical computer from inside of the #11 lab and from there I can now join it to the internal lab domain for further testing. I could of course re-image the device but as it's a shared device (aka the kids) I won't be doing that this time. and after the reboot you can login as a user that has Remote Desktop access and do whatever testing you wanted to carry out on real physical hardware. Install the ConfigMgr client... Step 5. Once done testing, set your lab back to Private Network Now that you are done testing, don't forget to set your labs network connection back to Private Network. This will avoid problems with networks getting crossed or devices talking to each other that shouldn't be. And don't forget to click Apply that's it, until next time, cheers niall.
-

Configuring BitLocker in Intune - Part 2. Automating Encryption
anyweb replied to anyweb's topic in Microsoft Intune
thanks @olavrb this is a good contribution, please keep them coming, as regards your profile pic, you need at least 10 posts to be able to change it, cheers ! niall -
Just wanted to follow up and let you know I have had great success utilizing your script.. the error checking is superb.. thank you for the work and troubleshooting you have done to vet your script.. you are a life saver!! great to hear it ! and thanks for the kind words @Jerzystransfer
- 242 replies
-
- 1702
- forced upgrade
-
(and 2 more)
Tagged with:
-

Configuring BitLocker in Intune - Part 2. Automating Encryption
anyweb replied to anyweb's topic in Microsoft Intune
sure post your updated code here -
why are you still using and even considering moving SCCM 2012 SP2 into Azure ? this version of ConfigMgr is out of mainstream support and is on extended support currently. https://support.microsoft.com/en-us/lifecycle/search/1060 if you want to use ConfigMgr in Azure then you'll need to be on a Current Branch release see - https://docs.microsoft.com/en-us/configmgr/core/understand/configuration-manager-on-azure
-
can you give some details of what you were doing here exactly and what type of drive D:\ is ?
-
you also need to remove any encryption on those devices before implementing BitLocker.
-

IP Helper question
anyweb replied to twidener's topic in System Center Configuration Manager (Current Branch)
iphelpers should point to where you intend to PXE boot from, so from the local (nearest) distribution point hosting a WDS role -
it's trying to copy a file (CM_site.mdf), not a folder. is the file in the source and target location ?
- 14 replies
-
- mandatory profiles
- wondows 10
-
(and 36 more)
Tagged with:
- mandatory profiles
- wondows 10
- cb1910
- sccm
- cross-forest
- multi-domain
- sccm
- cmg
- azure
- sup
- client
- sccm
- dp
- office 365 updates
- query or collection in sccm
- gpo
- sccm cb
- database
- sccm cmdlets
- sccm client
- powershell
- wmi
- sccm
- client settings
- console
- dell
- 7212
- imaging
- osd
- defaultuser0
- configmgr
- sccm
- admin tools
- current branch
- manageengine
- patch connect plus
- configuration manager
- non microsoft updates
-
are you failing with the same errors as before ?
- 14 replies
-
- mandatory profiles
- wondows 10
-
(and 36 more)
Tagged with:
- mandatory profiles
- wondows 10
- cb1910
- sccm
- cross-forest
- multi-domain
- sccm
- cmg
- azure
- sup
- client
- sccm
- dp
- office 365 updates
- query or collection in sccm
- gpo
- sccm cb
- database
- sccm cmdlets
- sccm client
- powershell
- wmi
- sccm
- client settings
- console
- dell
- 7212
- imaging
- osd
- defaultuser0
- configmgr
- sccm
- admin tools
- current branch
- manageengine
- patch connect plus
- configuration manager
- non microsoft updates
-
well you cannot have two different disk encryption methods at the same time so if you want to move to BitLocker (good choice) then you'll first need to completely remove whatever encryption that McAfee has put in place. Once that is done and the McAfee agent is removed you can enforce BitLocker easily with Configuration Manager, check out my blog post here for guidance. https://www.niallbrady.com/2019/11/13/want-to-learn-about-mbam-integrated-with-microsoft-endpoint-manager-configuration-manager/
-
normally you should use service accounts, but in your case, your sccm login is probably what you need, try it...
- 14 replies
-
- mandatory profiles
- wondows 10
-
(and 36 more)
Tagged with:
- mandatory profiles
- wondows 10
- cb1910
- sccm
- cross-forest
- multi-domain
- sccm
- cmg
- azure
- sup
- client
- sccm
- dp
- office 365 updates
- query or collection in sccm
- gpo
- sccm cb
- database
- sccm cmdlets
- sccm client
- powershell
- wmi
- sccm
- client settings
- console
- dell
- 7212
- imaging
- osd
- defaultuser0
- configmgr
- sccm
- admin tools
- current branch
- manageengine
- patch connect plus
- configuration manager
- non microsoft updates
-
what account was used before with the database mentioned ?
- 14 replies
-
- mandatory profiles
- wondows 10
-
(and 36 more)
Tagged with:
- mandatory profiles
- wondows 10
- cb1910
- sccm
- cross-forest
- multi-domain
- sccm
- cmg
- azure
- sup
- client
- sccm
- dp
- office 365 updates
- query or collection in sccm
- gpo
- sccm cb
- database
- sccm cmdlets
- sccm client
- powershell
- wmi
- sccm
- client settings
- console
- dell
- 7212
- imaging
- osd
- defaultuser0
- configmgr
- sccm
- admin tools
- current branch
- manageengine
- patch connect plus
- configuration manager
- non microsoft updates
-
look in SQL under logins, see what logins are there, add your account as SQL SysAdmin if you are not sure what to do
- 14 replies
-
- mandatory profiles
- wondows 10
-
(and 36 more)
Tagged with:
- mandatory profiles
- wondows 10
- cb1910
- sccm
- cross-forest
- multi-domain
- sccm
- cmg
- azure
- sup
- client
- sccm
- dp
- office 365 updates
- query or collection in sccm
- gpo
- sccm cb
- database
- sccm cmdlets
- sccm client
- powershell
- wmi
- sccm
- client settings
- console
- dell
- 7212
- imaging
- osd
- defaultuser0
- configmgr
- sccm
- admin tools
- current branch
- manageengine
- patch connect plus
- configuration manager
- non microsoft updates
-
check the username/password specified in sql, that's where it's failing, see below snippet... ERROR: Failed to restore databases. $$<Configuration Manager Setup><12-13-2019 14:41:31.500+00><thread=3800 (0xED8)> *** [28000][18456][Microsoft][SQL Server Native Client 11.0][SQL Server]Login failed for user 'sitename\user'. cheers niall
- 14 replies
-
- mandatory profiles
- wondows 10
-
(and 36 more)
Tagged with:
- mandatory profiles
- wondows 10
- cb1910
- sccm
- cross-forest
- multi-domain
- sccm
- cmg
- azure
- sup
- client
- sccm
- dp
- office 365 updates
- query or collection in sccm
- gpo
- sccm cb
- database
- sccm cmdlets
- sccm client
- powershell
- wmi
- sccm
- client settings
- console
- dell
- 7212
- imaging
- osd
- defaultuser0
- configmgr
- sccm
- admin tools
- current branch
- manageengine
- patch connect plus
- configuration manager
- non microsoft updates
-
thanks for sharing, please do let me know how you get on with this.
- 242 replies
-
- 1702
- forced upgrade
-
(and 2 more)
Tagged with:
-
hiya i didn't see that problem (see part 2 of my videos here) https://www.niallbrady.com/2019/12/10/learn-about-mbam-integration-in-microsoft-endpoint-configuration-manager-version-1910-part-2-configure-portals/ however i have one lab with the cert issue you reported on technet and your workaround didn't work for me, fyi cheers niall
-
thanks! yes you could check for the ip range that your network cables use (as opposed to wireless), and detect based on that, all networks are different so you'll have to customize it somehow to suit your environment cheers niall
- 242 replies
-
- 1702
- forced upgrade
-
(and 2 more)
Tagged with: