Search the Community
Showing results for tags 'Single Sign-On'.
-
I've created an PDF that contains the content of the series I did about integrating Microsoft Intune and System Center 2012 R2 Configuration Manager with Single Sign-On. All the following parts are covered in the PDF: How to integrate Microsoft Intune and System Center 2012 R2 Configuration Manage...
-
- Microsoft Intune
- Configuration Manager
-
(and 4 more)
Tagged with:
-
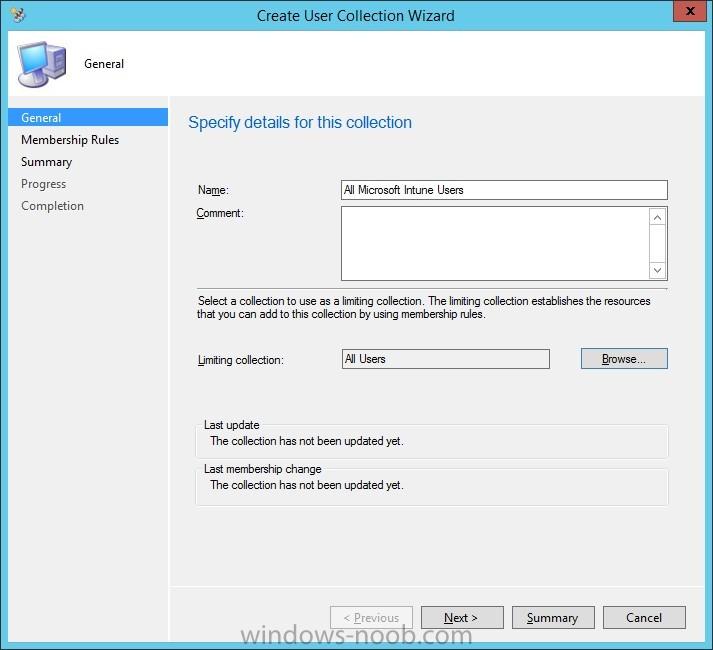
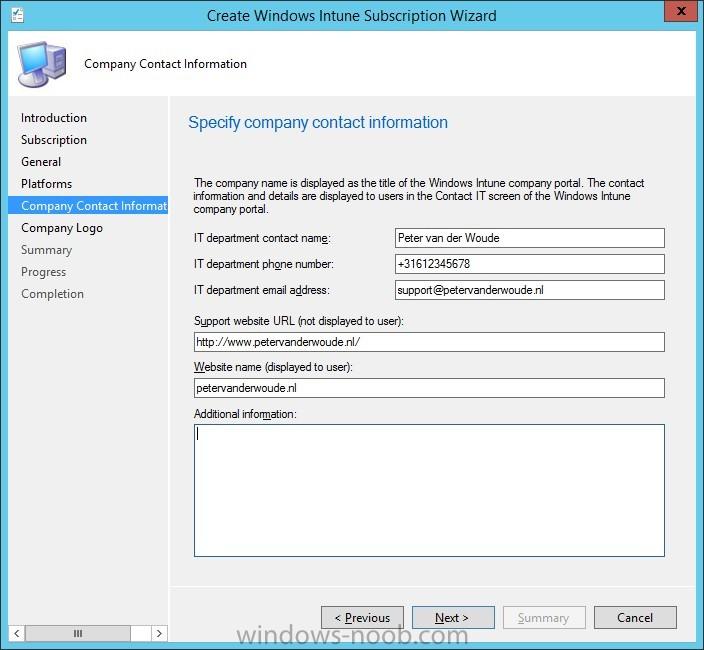
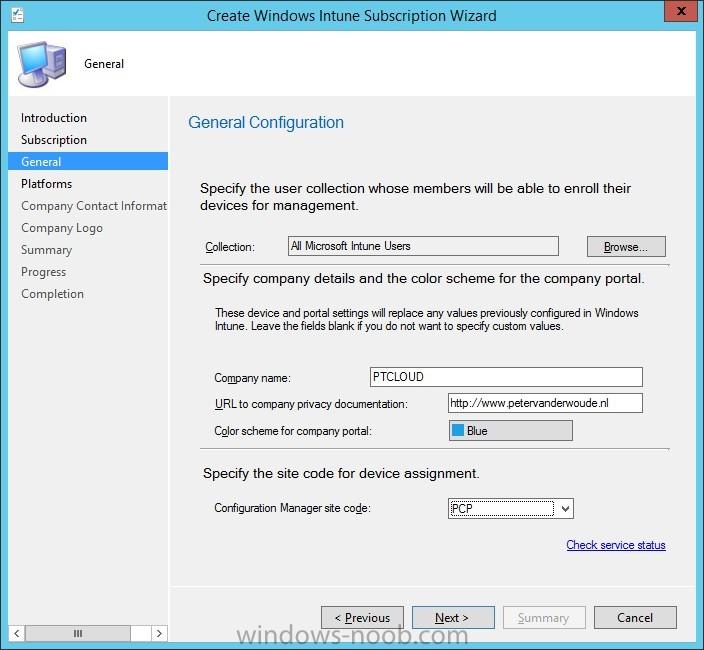
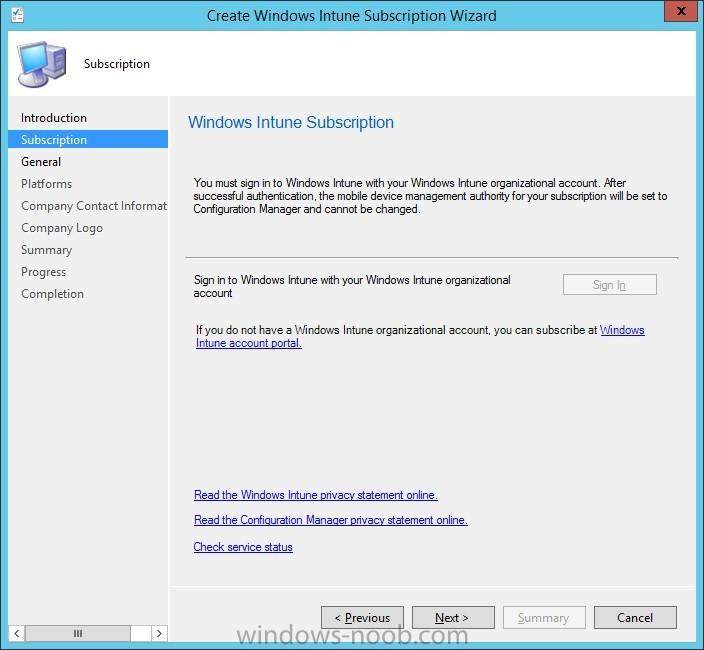
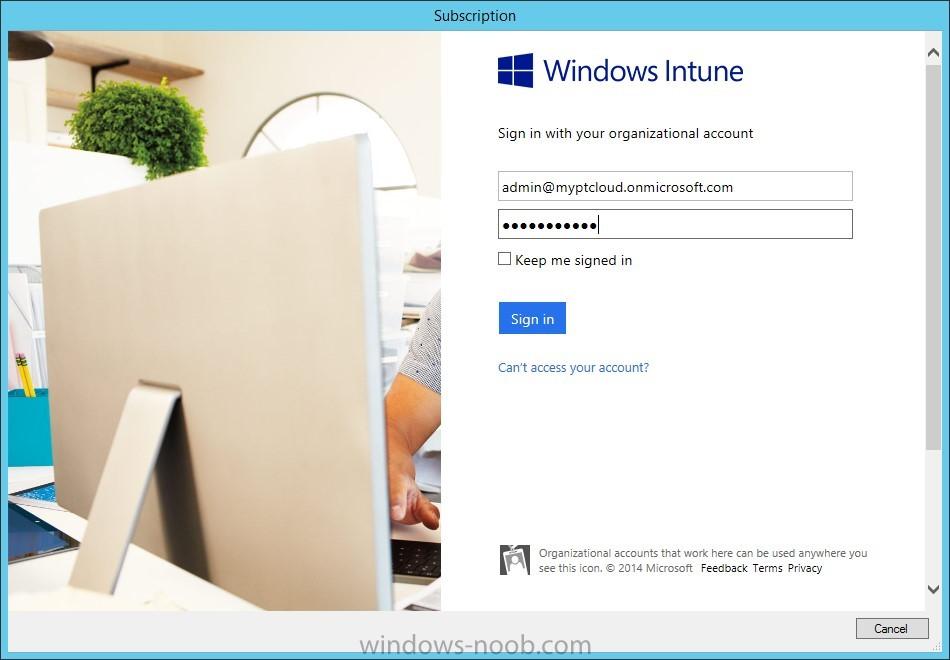
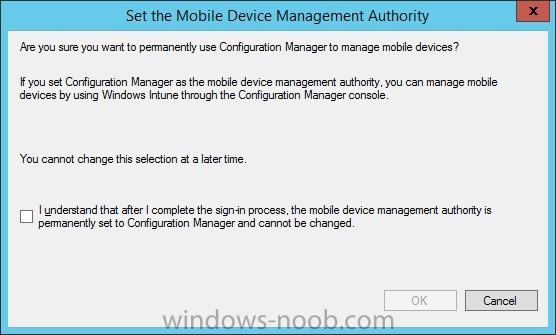
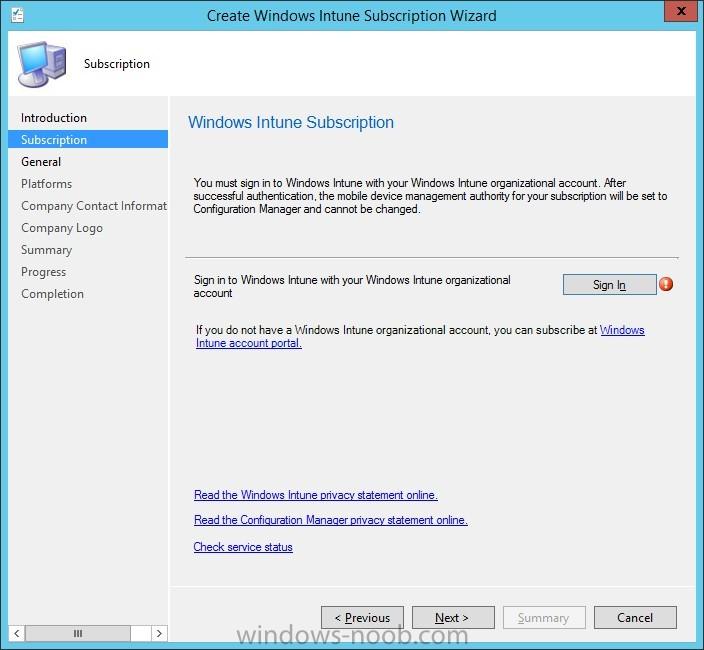
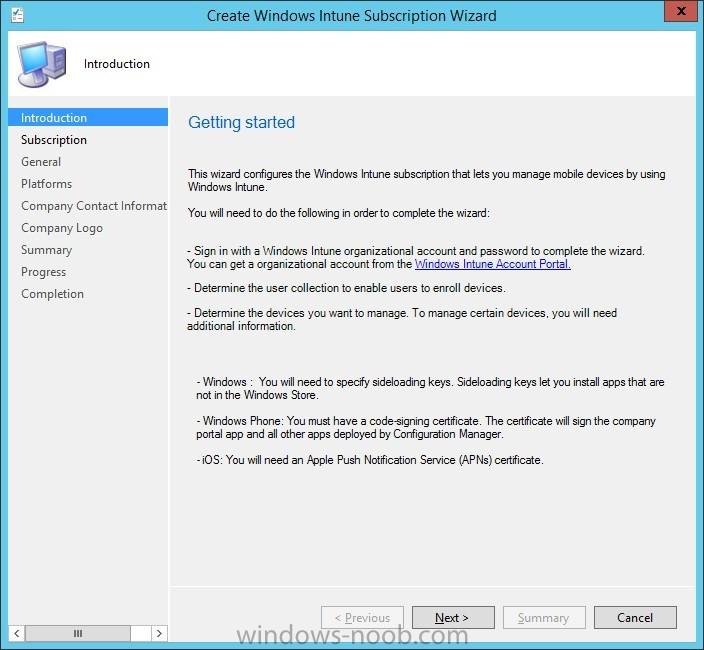
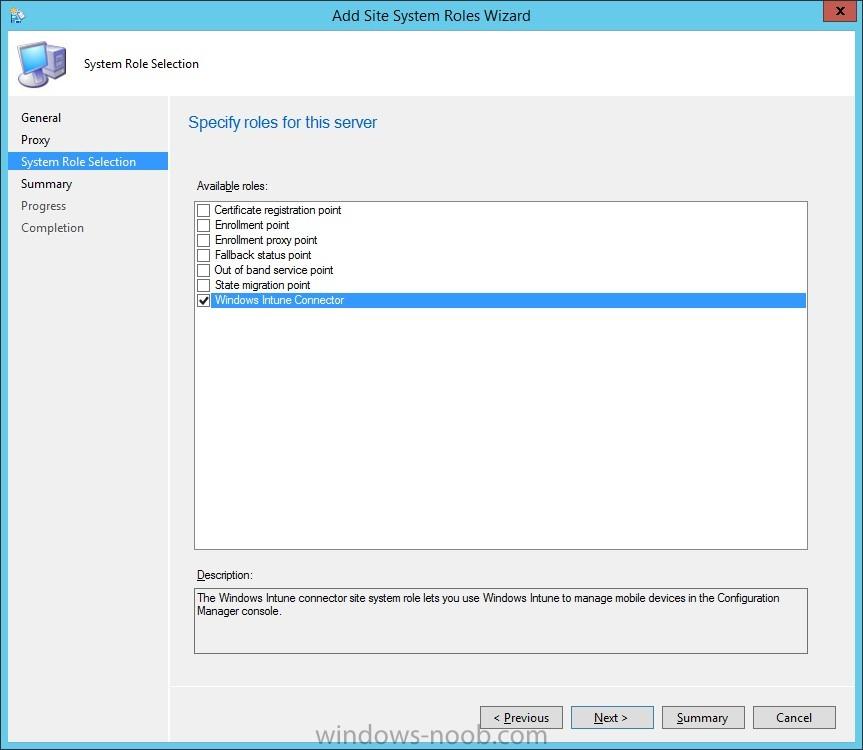
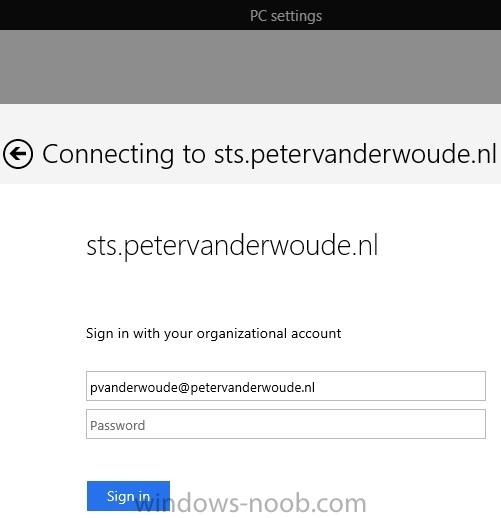
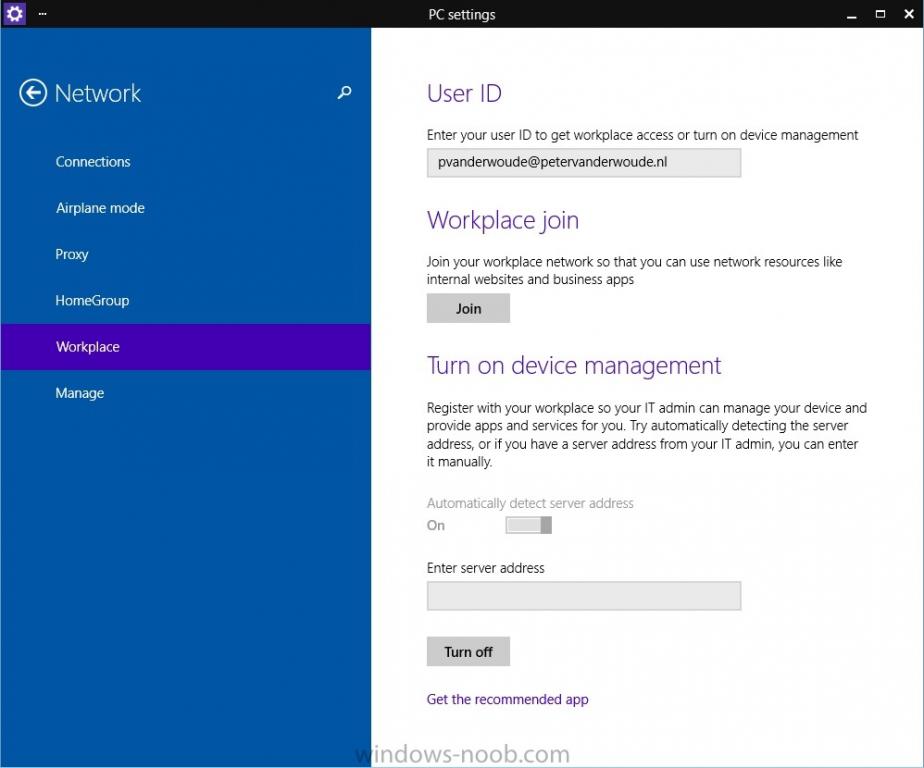
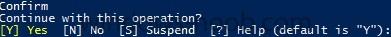
In the first part of this blog series I went through the introduction and the prerequisites, in the second part I went through the installation and configuration of AD FS and in the third part I went through the directory synchronization. This fourth part of the blog series will finally be about Con...
-
- Microsoft Intune
- Configuration Manager
-
(and 3 more)
Tagged with:
-
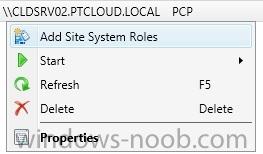
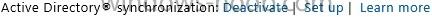
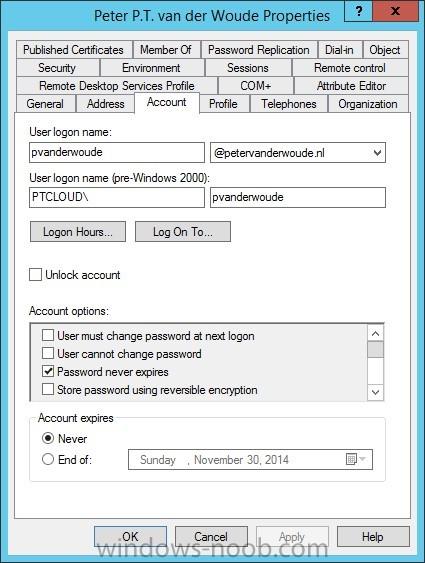
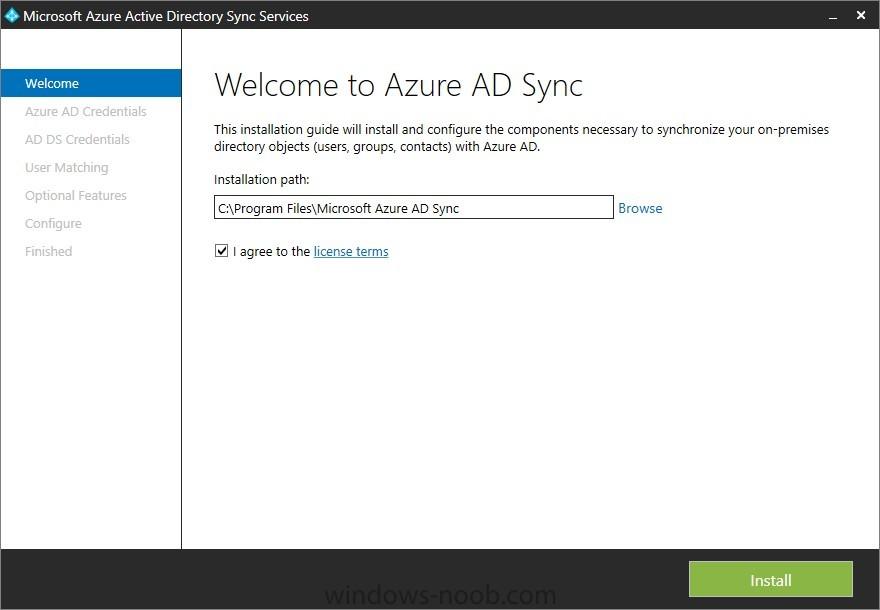
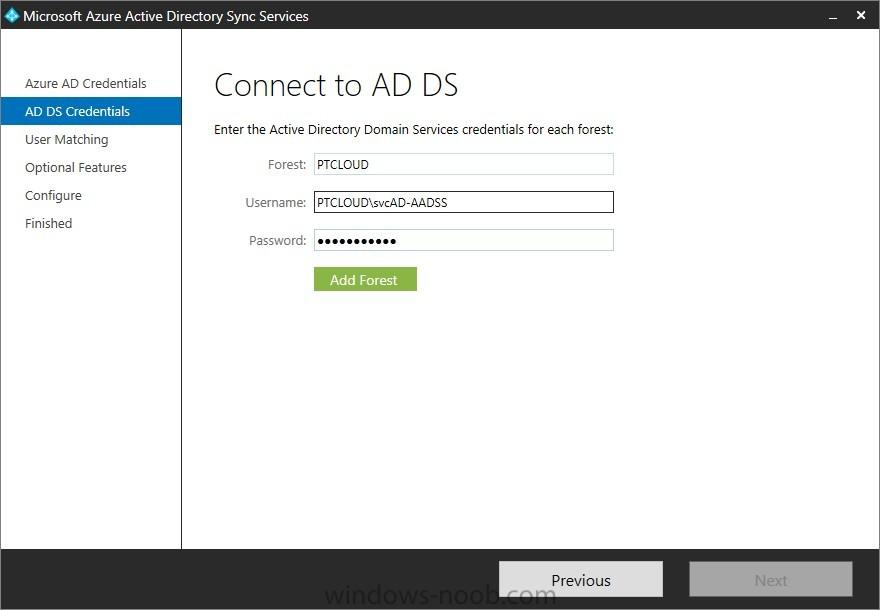
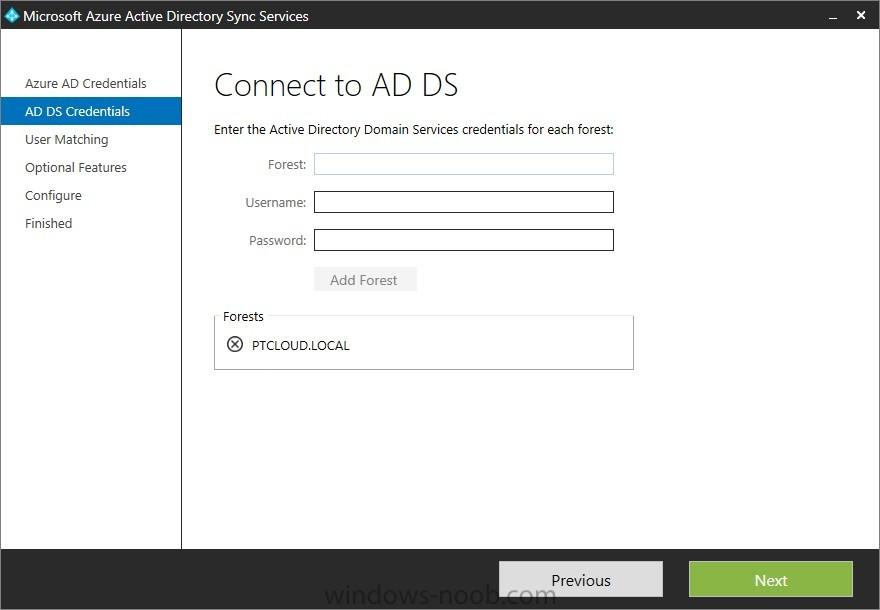
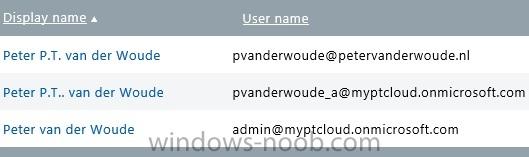
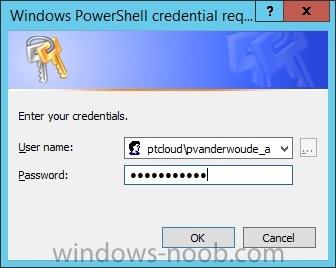
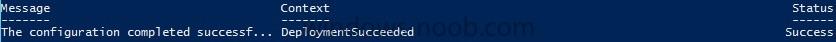
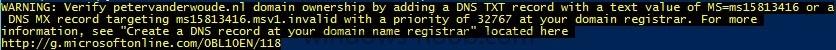
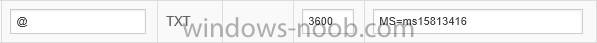
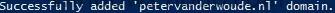
In the first part of this blog series I went through the introduction and the prerequisites and in the second part I went through the installation and configuration of AD FS. This third part of the blog series will be all about configuring, configuring and configuring. First it's required to add the...
-
- Microsoft Intune
- Configuration Manager
-
(and 4 more)
Tagged with:
-
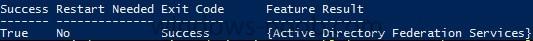
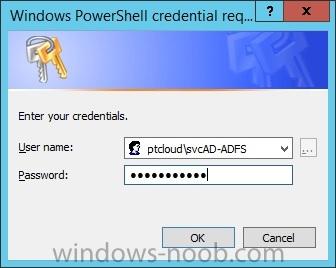
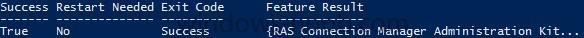
In the first part of this blog series I went through the introduction and the prerequisites. This second part of the blog series will be all about installing and configuring Active Directory Federation Services (AD FS) and the AD FS proxy, which is the Web Application Proxy (WAP) in Server 2012 R2....